Existence and Uniqueness Analysis in ABM Verification: A Foundational Framework for Credible Computational Models in Biomedicine
This article provides a comprehensive guide to existence and uniqueness analysis, a critical but often overlooked component of Agent-Based Model (ABM) verification.
Existence and Uniqueness Analysis in ABM Verification: A Foundational Framework for Credible Computational Models in Biomedicine
Abstract
This article provides a comprehensive guide to existence and uniqueness analysis, a critical but often overlooked component of Agent-Based Model (ABM) verification. Tailored for researchers, scientists, and drug development professionals, we demystify the foundational mathematical concepts and present a step-by-step methodological framework for practical implementation. The content bridges theoretical principles with real-world application, covering troubleshooting strategies for common numerical instabilities and validation techniques to integrate this analysis within broader model credibility assessments like VV&UQ. By establishing rigorous verification practices, this guide aims to empower the development of high-fidelity, regulatory-ready in silico models for predictive oncology, immunology, and therapeutic development.
Why Existence and Uniqueness Matter: The Bedrock of Credible Agent-Based Models
Defining Existence and Uniqueness in the Context of Stochastic ABMs
Frequently Asked Questions (FAQs) and Troubleshooting Guides
FAQ: Core Theoretical Concepts
Q1: What do "existence and uniqueness" mean for a Stochastic Agent-Based Model? In the context of Stochastic ABMs, "existence" refers to the mathematical guarantee that a solution to the model's governing equations exists for a given set of initial conditions and parameters. "Uniqueness" means that this solution is the only possible one; no other fundamentally different behaviors can emerge from the same starting point. Establishing these properties is a foundational step in model verification, ensuring that your model's dynamics are well-defined and not subject to arbitrary numerical instabilities [1].
Q2: Why is proving existence and uniqueness particularly challenging for Stochastic ABMs compared to other model types? Stochastic ABMs present unique challenges due to their inherent nonlinearity, path-dependence, and the complex interactions between discrete agents. Unlike simpler models, the governing equations often involve locally one-sided Lipschitz conditions and lack the global monotonicity that simplifies analysis in other dynamical systems. Furthermore, the discrete stochastic interactions can create discontinuities that violate the smoothness assumptions of classical theorems [1].
Q3: My ABM produces chaotic-looking results. How can I tell if this is genuine complexity or a numerical artifact? This is a critical distinction in verification. Begin by implementing sensitivity analysis on your numerical integrator's step size. If the qualitative behavior stabilizes as the step size decreases, it suggests genuine complexity. Conversely, if wild fluctuations persist or change unpredictably, it is likely a numerical artifact, indicating that your model may violate local uniqueness conditions or that the numerical method is inappropriate for your system's stiffness [2].
Troubleshooting Guide: Common Errors and Solutions
Problem: Simulation runs yield dramatically different outcomes from identical initial conditions. This symptom directly points to a potential failure of uniqueness or a severe numerical instability.
- Possible Cause 1: Violation of a local Lipschitz condition in the agent interaction rules.
- Solution: Check if your agent decision functions or interaction kernels have discontinuous jumps or are not locally one-sided Lipschitz. Reformulate these rules to be smooth, or apply a more general existence theorem that accommodates your specific condition [1].
- Possible Cause 2: Inadequate numerical method for the underlying stochastic differential equations.
- Solution: The standard Euler-Maruyama method may be insufficient. Consider implementing Euler's polygonal line method, which has been proven effective for establishing existence and uniqueness under locally one-sided Lipschitz conditions [1].
- Investigation Protocol:
- Parameter Smoothing: Temporarily replace all
if-then-elserules in agent decisions with smooth sigmoid functions. Re-run the simulation. - Path Sampling: If results converge, the original discontinuity is the cause. If not, sample and plot multiple agent trajectories to identify where they diverge.
- Method Comparison: Re-implement the model using a higher-order stochastic numerical method (e.g., Milstein method) and compare the outcome distributions.
- Parameter Smoothing: Temporarily replace all
Problem: The model fails to produce a stable solution or "blows up" in finite time. This often indicates a failure of the existence conditions, where the model's dynamics do not permit a bounded solution.
- Possible Cause: The model's coefficients do not satisfy the necessary growth conditions, allowing agent states (e.g., wealth, social pressure) to become infinite.
- Solution: Introduce a mathematical constraint that bounds the agent state variables. This can often be achieved by adding a stabilizing term that mimics carrying capacity or budget constraints, ensuring the
pth moment boundedness of solutions [1]. - Investigation Protocol:
- Moment Tracking: Implement real-time tracking of the mean and variance of key agent state variables.
- Growth Analysis: Log the maximum and minimum values of these states. The point at which they trend towards infinity is the failure point.
- Constraint Implementation: Add a soft maximum limit to the critical variables using a bounding function and verify that the solution stabilizes.
Problem: Difficulty in matching simulated data to real-world data for validation. This is a core challenge in moving from verification to validation.
- Possible Cause: The model has not been adequately validated through explicit comparison of real and simulated data. A model can be mathematically sound (existence and uniqueness) but still not reflect reality [3].
- Solution: Employ the validation framework of explicitly comparing real and simulated data. This process is more fundamental than calibration for ensuring a model tells you something about the real world [3].
- Investigation Protocol:
- Data Confrontation: Identify specific, quantifiable outputs from your model and obtain corresponding real-world data.
- Comparison and Iteration: Systematically compare these outputs in tables or figures. Use the discrepancies to refine the model's mechanisms, not just its parameters [3].
Experimental Protocols for Verification
Protocol 1: Numerical Verification of Existence via Euler's Polygonal Line Method
Objective: To provide numerical evidence for the existence of a solution by implementing a stable discretization method.
Methodology:
- Discretization: Apply Euler's polygonal line method to the stochastic differential equations governing agent dynamics. This method constructs an approximate solution by creating a polygonal line through computed points [1].
- Convergence Testing: Run simulations with a sequence of decreasing time steps (e.g.,
dt = 0.1, 0.01, 0.001). - Analysis: Observe if the sequence of approximate solutions converges to a limiting process. Qualitative and quantitative stability across step sizes supports the existence of a true, continuous-time solution.
Protocol 2: Empirical Validation Through Real vs. Simulated Data Comparison
Objective: To validate the model by confronting its outputs with real-world data, moving beyond mere mathematical verification.
Methodology:
- Output Selection: Define one or more key outputs from your ABM (e.g., population distribution, market share over time).
- Data Collection: Gather corresponding empirical data from historical records, surveys, or other studies.
- Explicit Comparison: Create a combined figure or table that places the real data and the simulated data side-by-side. This direct visual and statistical comparison is the cornerstone of empirical validation [3].
- Goodness-of-Fit: Use statistical tests (e.g., Kolmogorov-Smirnov, Mean Squared Error) to quantify the fit between the simulated and real data.
Model Verification Workflow
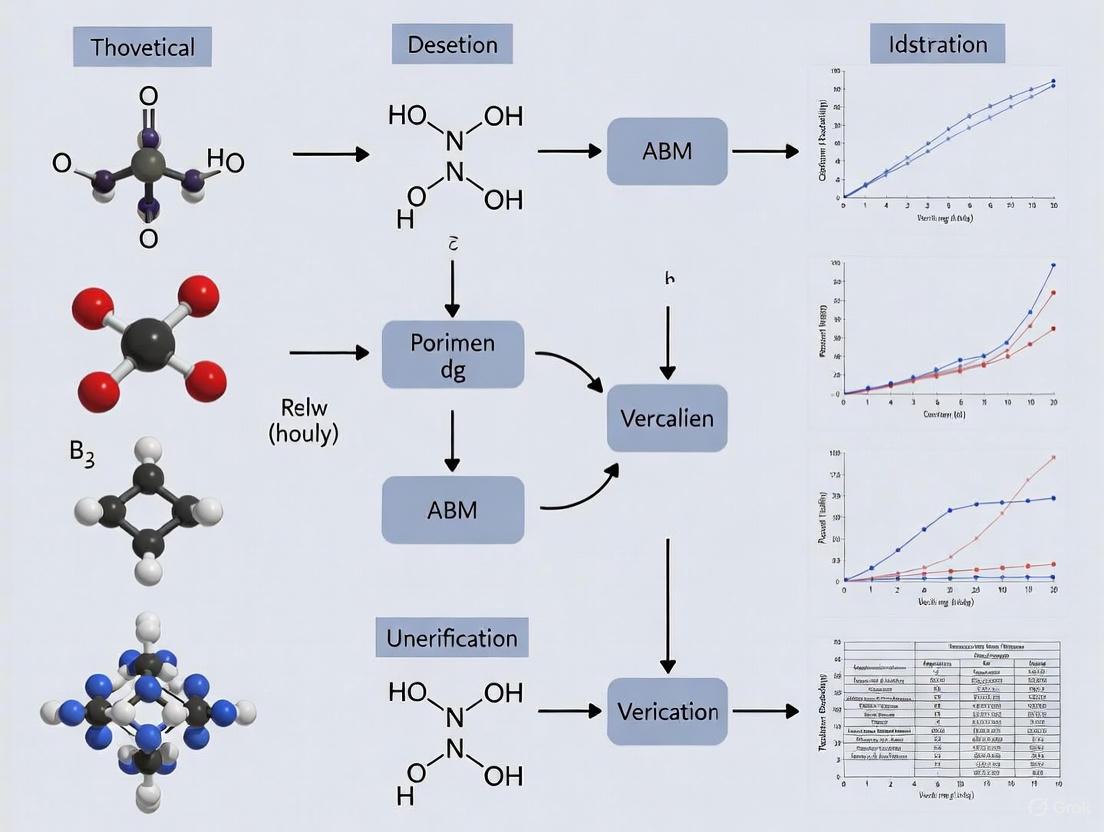
The following diagram illustrates the logical relationship and process flow for establishing the existence and uniqueness of solutions in Stochastic ABMs, leading to empirical validation.
The Scientist's Toolkit: Research Reagent Solutions
The following table details key methodological "reagents" and their function in the analysis of existence and uniqueness for Stochastic ABMs.
| Research Reagent | Function in Analysis |
|---|---|
| Locally One-Sided Lipschitz Condition | A generalized assumption on model coefficients that allows growth while still permitting the proof of existence and uniqueness, replacing the more restrictive monotone condition [1]. |
| Euler's Polygonal Line Method | A numerical technique used not just for simulation, but as a constructive method to prove the existence of solutions for SDEs with complex coefficients [1]. |
| p-th Moment Boundedness | A mathematical property demonstrating that the solution's statistical moments (mean, variance) remain finite over time, providing evidence of a stable, non-explosive solution [1]. |
| Empirical Validation Bibliography | A curated collection of ABM research that explicitly compares real and simulated data, serving as a benchmark for validation practices and methodology [3]. |
| Sensitivity Analysis | A process of testing the model's response to changes in parameters and numerical step sizes, helping to distinguish true emergent complexity from numerical artifacts [2]. |
Quantitative Data on Verification and Validation
The table below summarizes key concepts and their quantitative or qualitative benchmarks relevant to the verification process.
| Concept | Benchmark / Threshold | Purpose in Verification |
|---|---|---|
| Contrast (Enhanced) - WCAG AAA | 7:1 (standard text)4.5:1 (large text) | A benchmark for ensuring visualizations and diagrams have sufficient color contrast for readability and accessibility, which is critical for accurately interpreting model output [4]. |
| Numerical Convergence | Stable solution with decreasing step size (e.g., dt -> 0) | Provides numerical evidence for the existence of a solution. A model whose behavior wildly changes with step size may not have a unique solution. |
| p-th Moment Boundedness | Finite variance and higher moments over time | Demonstrates solution stability and is a key property often established alongside existence and uniqueness theorems [1]. |
| Empirical Validation | Explicit comparison in figure/table | The fundamental test for determining if a verified model actually tells us something about the real world, moving from mathematical correctness to scientific utility [3]. |
The Critical Role in Regulatory Acceptance and In Silico Trials
Foundational Concepts: Verification, Validation, and Credibility
What is the difference between verification and validation (V&V) for an Agent-Based Model (ABM)?
Verification and validation are distinct but complementary processes critical for establishing ABM credibility.
- Verification answers the question "Are we building the model right?" It is the process of ensuring that the computational model correctly implements its intended mathematical and conceptual design, and that there are no errors in the code or the numerical solutions [5] [2]. Key steps include checking for coding bugs and ensuring numerical accuracy.
- Validation answers the question "Are we building the right model?" It is the process of determining the degree to which the model is an accurate representation of the real-world biology or clinical outcome from the perspective of the model's intended use [2] [6]. This involves comparing model predictions with independent experimental or clinical data.
Why is the "Context of Use" (COU) so important for regulatory submission?
The Context of Use (COU) is a formal definition that specifies the specific role and scope of the computational model in addressing a regulatory question of interest [5] [6]. It is the foundational first step in any credibility assessment, as defined by standards like ASME V&V 40-2018 [5]. The COU dictates the required level of model credibility. For instance, a model used to inform a go/no-go decision on a drug target will require a different level of validation than a model used as primary evidence of efficacy in a marketing authorization application. All subsequent verification, validation, and uncertainty quantification activities are scaled based on the COU and its associated risk [5] [6].
What is a "Credibility Assessment Plan" and what are its key components?
A Credibility Assessment Plan is a risk-informed strategy, often based on standards like ASME V&V 40-2018, that outlines the specific activities and acceptance criteria for demonstrating a model's fitness for its Context of Use [5] [6]. The core components are outlined in the workflow below:
Troubleshooting ABM Verification: Existence and Uniqueness
How do I verify the "existence" and "uniqueness" of my ABM's solution?
Existence and Uniqueness analysis is a core component of the deterministic verification of ABMs [7]. The following guide helps diagnose and resolve common failures in this analysis.
| Symptom | Potential Root Cause | Recommended Corrective Action |
|---|---|---|
| Simulation fails to produce an output or crashes for a valid input set. | Violation of Existence: Model rules or parameters lead to an unrecoverable state (e.g., division by zero, an agent type going extinct). | 1. Review agent interaction rules for logical errors. 2. Implement safeguards in the code (e.g., check for zero before division). 3. Validate input parameter ranges against known biological constraints [7]. |
| The same initial seed and inputs produce meaningfully different outputs across runs. | Violation of Uniqueness: Numerical instabilities, use of uninitialized variables, or parallel computing race conditions. | 1. Fix the random seed and verify it is correctly applied to all stochastic processes. 2. Check for floating-point rounding errors in critical calculations. 3. Ensure all variables are properly initialized before the main simulation loop [7]. |
| Small changes in an input parameter cause large, discontinuous jumps in model output. | Numerical Ill-Conditioning: The model is overly sensitive to specific parameters, indicating potential structural or stability issues. | 1. Perform a sensitivity analysis (e.g., LHS-PRCC) to identify problematic parameters. 2. Review the biological rationale for the sensitive parameters and interactions. 3. Consider model simplification or re-formulation in the sensitive areas [7]. |
What is the standard workflow for deterministic verification of an ABM?
The verification workflow involves several automated and manual checks to ensure model robustness. The following protocol, based on the Model Verification Tools (MVT) computational framework, outlines the key steps [7].
Protocol: Deterministic Verification Workflow for ABMs
Objective: To verify that the ABM is implemented correctly and operates in a robust, numerically stable manner.
Materials:
- The ABM software and computational environment.
- Model Verification Tools (MVT) suite or equivalent custom scripts [7].
- A defined set of model outputs of interest (e.g., cell count, cytokine concentration).
Method:
- Existence and Uniqueness Analysis:
- Run the model across the entire defined range of input parameters to ensure it always produces a valid output (Existence).
- Execute multiple runs with the exact same initial random seed and input parameters. Compare key outputs to ensure they are identical (Uniqueness). The tolerated variation should be minimal, attributable only to numerical rounding [7].
- Time Step Convergence Analysis:
- Run the same simulation scenario with progressively smaller time-step lengths (e.g., 1.0, 0.5, 0.1, 0.01).
- Calculate the percentage discretization error (eqi) for a key output quantity (e.g., peak value) relative to the result from the smallest, computationally tractable reference time-step (i). The model is considered converged if *eqi < 5% for the time-step used in production [7].
- Smoothness Analysis:
- For all output time series, compute the coefficient of variation (D) as the standard deviation of the first difference of the series, scaled by the absolute mean.
- Use a moving window (e.g., k=3) for this calculation. A high value of D indicates a higher risk of stiffness, singularities, or discontinuities in the solution that may warrant investigation [7].
- Parameter Sweep Analysis:
- Use global sensitivity analysis techniques, such as Latin Hypercube Sampling combined with Partial Rank Correlation Coefficient (LHS-PRCC), to sample the input parameter space.
- The goal is to confirm the model is not ill-conditioned and to identify input parameters to which the outputs are abnormally sensitive [7].
Tools and Materials for ABM Verification and Validation
What tools are available to help automate the verification of ABMs?
The Model Verification Tools (MVT) is an open-source software suite specifically designed to facilitate the verification of discrete-time stochastic models like ABMs [7]. It provides a user-friendly interface to perform key deterministic verification steps.
Research Reagent Solutions: Key Computational Tools for ABM Credibility
| Tool / Resource | Function | Relevance to ABM Credibility |
|---|---|---|
| Model Verification Tools (MVT) [7] | An open-source Python-based suite that automates key verification steps. | Provides automated analysis for Existence, Uniqueness, Time Step Convergence, Smoothness, and Parameter Sweeps. |
| ASME V&V 40-2018 Standard [5] [6] | A technical standard for assessing credibility of computational models in medical device development, adaptable to drug development. | Provides the overarching risk-informed framework for planning and reporting credibility assessments, including definitions for COU and model risk. |
| Latin Hypercube Sampling & PRCC (LHS-PRCC) [7] | A global sensitivity analysis technique implemented within MVT and other packages. | Used in Parameter Sweep analysis to identify which input parameters have the greatest influence on model outputs, highlighting potential ill-conditioning. |
| Universal Immune System Simulator (UISS) [6] | An agent-based modeling platform designed to simulate immune system responses. | Serves as an example of an ABM framework for which a comprehensive Credibility Assessment Plan has been developed for a specific Context of Use (TB treatment) [6]. |
How is a risk analysis performed for an ABM used in a regulatory submission?
The risk analysis is a critical step that directly influences the level of V&V required. Risk is defined as a combination of Model Influence and Decision Consequence [5] [6]. The following table helps categorize these elements.
Table: Framework for ABM Risk Analysis in Regulatory Submissions
| Model Influence (Contribution to Decision) | Decision Consequence (Impact of an Incorrect Prediction) |
|---|---|
| Low: The ABM provides supportive, exploratory insights. Other evidence is primary. | Low: Minor impact on development timeline or internal resource allocation. |
| Medium: The ABM is used to inform critical development choices (e.g., dose selection, trial design). | Medium: Potential for a large financial loss or a significant delay in a development program. |
| High: The ABM provides the primary or sole evidence of safety/efficacy for a regulatory decision. | High: Potential for adverse patient outcomes, misinformed clinical use, or product recall. |
The overall model risk is determined by considering both factors. A high-influence model supporting a high-consequence decision necessitates the most rigorous and extensive V&V activities.
Distinguishing Model Verification from Model Validation
Frequently Asked Questions (FAQs)
FAQ 1: What is the fundamental difference between verification and validation? Verification is the process of confirming that a computational model implements its underlying equations and intended behaviors correctly and without technical errors. It answers the question: "Are we building the model right?" In contrast, validation determines whether the model is an accurate representation of the real-world system it is intended to simulate. It answers the question: "Are we building the right model?" [8] [9]
FAQ 2: Why is the distinction especially critical for Agent-Based Models (ABMs) in biomedical research? ABMs simulate how population-level behaviors emerge from the interactions of individual components (agents) [10]. This complexity means that a model can be perfectly verified (bug-free code) yet still be invalid if the rules governing agent behavior do not reflect biological reality. Establishing that a model's outcomes are a unique and credible consequence of its mechanistic rules is a core challenge in ABM research [11] [12].
FAQ 3: How does the "Context of Use" influence validation? The level of rigor required for both verification and validation is determined by the model's Context of Use—the specific role and impact of the model in informing a decision, especially in a regulatory setting [8]. A model used for early-stage hypothesis generation will have different validation requirements than one used to support a clinical trial design or a regulatory submission for a new drug.
FAQ 4: What are common signs that my ABM may not be properly validated? Common indicators include an over-reliance on face-validity (the model "looks right" but isn't tested quantitatively) and outcome measures that are only loosely tied to the underlying mechanisms. Another sign is an inability to replicate core emergent phenomena observed in real-world data when initial conditions are slightly altered [11].
Troubleshooting Guides
Issue 1: Model Produces Unstable or Inconsistent Results
Problem: Your ABM generates vastly different outcomes across simulation runs with identical parameters, suggesting potential implementation errors or true stochasticity that needs characterization.
Investigation Protocol:
- Verification Check: Ensure all random number generators are properly seeded to allow for reproducible results during the debugging phase.
- Sensitivity Analysis: Systematically vary key parameters one at a time to identify if specific inputs are causing the instability. This helps distinguish between coding errors and highly sensitive model dynamics.
- State-Space Exploration: For ABMs, it is often necessary to run multiple simulations (ensemble runs) to understand the distribution of possible outcomes, rather than expecting a single result from one run [10].
Issue 2: Failure to Replicate Key Empirical or Clinical Data
Problem: The macro-level patterns emerging from your ABM do not match the empirical data you are trying to model.
Investigation Protocol:
- Input Validation: Re-examine the empirical meaningfulness of your model's exogenous inputs, such as initial conditions, parameter estimates, and functional forms [9]. Are they grounded in appropriate biological data?
- Process Validation: Scrutinize the rules governing agent behavior and interaction. "If you didn't grow it, you didn't explain it" [9]. Ensure the mechanistic processes (biological, physical) represented in the model reflect real-world aspects critical for your context of use [9].
- Calibration and Fitting: Calibrate your model against a portion of your empirical data (in-sample fitting). Then, test its predictive power on a separate, withheld portion of the data (out-of-sample forecasting) to ensure you have not over-fitted the model [9].
Issue 3: Preparing an ABM for Regulatory Evaluation
Problem: You need to demonstrate the credibility of your model for use in the regulatory evaluation of a biomedical product.
Investigation Protocol:
- Define Context of Use: Formally document the specific regulatory question your model is intended to address. This is the foundational step that determines all subsequent V&V activities [8].
- Conduct Risk-Based Analysis: Perform an analysis to identify the model's high-risk assumptions—those that most significantly impact the output relevant to the Context of Use. Focus your V&V efforts on these areas [8].
- Execute a V&V Plan: Follow a structured framework for credibility assessment, which includes:
- Verification: Demonstrate the software is implemented correctly.
- Validation: Provide evidence the model is sufficiently accurate for its Context of Use.
- Uncertainty Quantification: Characterize the uncertainty in model predictions [8].
Core Concepts & Workflow
The relationship between verification and validation, and their role in establishing model credibility, can be visualized as a sequential workflow.
Comparative Analysis: Verification vs. Validation
The table below provides a structured comparison to help distinguish these two critical processes.
| Aspect | Model Verification | Model Validation |
|---|---|---|
| Core Question | Are we building the model right? [9] | Are we building the right model? [9] |
| Primary Focus | Internal correctness; code and implementation [8] | External accuracy; match to real-world data [8] |
| Key Methods | Unit testing, code review, debugging, ensuring solutions to equations are unique and stable [13] | Input, process, and output validation; calibration against empirical data; historical data matching [9] |
| Relationship to Context of Use | Largely independent of the specific application. | Entirely dependent on the model's intended Context of Use [8]. |
| Analogy | Confirming a blueprint is followed correctly during construction. | Confirming the finished building meets the occupants' needs. |
The Scientist's Toolkit: Research Reagent Solutions
The following table details key methodological "reagents" and their functions in the verification and validation process.
| Research Reagent | Function in V&V Process |
|---|---|
| Sensitivity & Uncertainty Analysis (SA/UA) | A computational method to determine how variations in model inputs affect outputs. It is crucial for identifying high-risk parameters to target for validation [8]. |
| Ordinary/Partial Differential Equations (ODEs/PDEs) | Used in hybrid multi-scale models or to represent specific biological processes. Their well-established existence and uniqueness theorems provide a verification baseline for parts of the system [13] [12]. |
| Markov Decision Process (MDP) Formalism | A framework for modeling agent decision-making in uncertain environments. Formalizing agent rules as an MDP allows for rigorous analysis of emergent behavior and probabilistic verification [14]. |
| Empirical Validation Framework | A structured approach encompassing input, process, descriptive output, and predictive output validation to ensure the model is consistent with empirical data at multiple levels [9]. |
| In Silico Clinical Trials | The use of validated models to simulate clinical trials. This requires the highest degree of model credibility and is subject to rigorous regulatory scrutiny and V&V standards [8]. |
Frequently Asked Questions (FAQs)
Q1: What is solution verification in the context of Agent-Based Models (ABMs), and why is it critical for my research? Solution verification is the process of ensuring that your computational model is implemented correctly and produces numerically sound and reliable results. For ABMs, this involves specific analyses like existence and uniqueness to check that a solution exists for your input parameters and that it is the only possible solution, preventing ambiguous interpretations. Ignoring this can lead to instability and unreliable predictions, as your model might produce different outcomes under identical conditions or be overly sensitive to minor numerical changes, completely undermining its scientific and regulatory value [7] [15] [5].
Q2: I've validated my model against real-world data. Why do I still need to perform a uniqueness analysis? Validation checks if your model matches reality, while verification (including uniqueness analysis) checks if the model itself is built and solved correctly. A model can be well-validated but still be numerically unstable. Uniqueness analysis specifically guards against non-unique solutions and round-off errors due to the limited precision of computers. If ignored, your validated model could still produce different results on different computing platforms or with different random seeds, making its predictions fundamentally unreliable for high-stakes decisions like drug development [7] [16].
Q3: What are the most common symptoms of an unverified ABM that suffers from instability? If your ABM lacks proper solution verification, you may observe these common symptoms:
- Diverging Results: Simulation outputs differ significantly when run with the same parameters but on different machines or software versions.
- Extreme Sensitivity: Outputs change drastically with tiny variations in input parameters, indicating potential ill-conditioning.
- Non-Smooth Outputs: Time-series results show unexpected bucking, discontinuities, or stiffness, suggesting numerical errors in the solution process [7].
- Failure to Converge: Key model outputs do not stabilize when you reduce the simulation time-step [7].
Troubleshooting Guides
Problem: Non-Unique or Non-Reproducible Model Outputs
Description: Your model produces different results for the same initial conditions and parameters, making conclusions unreliable.
Diagnosis: This is a classic failure in deterministic verification, specifically related to existence and uniqueness.
Solution:
- Existence Check: Verify the model returns an output for all reasonable values in your input parameter space [7].
- Uniqueness Analysis: Run the model multiple times with identical input sets and the same pseudo-random number generator seed. The outputs should be identical, with at most a minimal variation determined by the numerical rounding algorithm of your computing platform [7].
- Code Verification: Check for programming errors, such as uninitialized variables or the inadvertent use of non-fixed random seeds.
Problem: Model is Overly Sensitive or Yields Ill-Conditioned Results
Description: Small, scientifically insignificant changes to an input parameter cause large, unpredictable swings in model outcomes.
Diagnosis: The model may be numerically ill-conditioned. This requires a parameter sweep analysis to map the model's behavior across its input space.
Solution:
- Parameter Sweep: Systematically sample the entire input parameter space to identify regions where the model fails to produce a valid solution or where the solution is valid but outside the expected range [7].
- Sensitivity Analysis: Employ robust sensitivity analysis techniques like LHS-PRCC (Latin Hypercube Sampling - Partial Rank Correlation Coefficient) or Sobol' method to quantitatively estimate the influence of each input parameter on the output. This helps distinguish true biological sensitivity from numerical instability [7].
Experimental Protocols for Verification
The table below summarizes key quantitative analyses for assessing your ABM's stability and reliability.
| Analysis Type | Key Metric | Target Threshold | Methodology |
|---|---|---|---|
| Time-Step Convergence Analysis [7] | Percentage discretization error: $e_{q}^{i} = \frac{{q^{i} - q^{i} }}{{q^{i} }}*100$ | Error < 5% | Run the model with progressively smaller time-steps (i). Compare output quantity (q) at each step to a reference value (q*) from the smallest tractable time-step. |
| Smoothness Analysis [7] | Coefficient of Variation (D) | Lower is better; no universal threshold. Evaluates risk. | Calculate the standard deviation of the first difference of the output time series, scaled by the absolute value of their mean, using a moving window (e.g., k=3). |
| Stochastic Verification (Consistency) [7] | Distributional similarity | Pass statistical tests (e.g., Kolmogorov-Smirnov) | Run multiple stochastic realizations (with different random seeds) and confirm that the outputs are consistent and belong to the same statistical distribution. |
The following workflow diagram illustrates the logical relationship between these verification steps and the consequences of their failure.
The Scientist's Toolkit: Essential Research Reagents for ABM Verification
This table details key computational "reagents" and tools essential for performing rigorous solution verification.
| Tool / Reagent | Function in Verification | Brief Explanation |
|---|---|---|
| Model Verification Tools (MVT) [7] | All-in-one suite for deterministic verification. | An open-source, Dockerized platform that automates key steps like existence, time-step convergence, smoothness, and parameter sweep analyses for discrete-time ABMs. |
| Pseudo-Random Number Generator (PRNG) | Uniqueness and stochastic verification. | A core component for stochastic ABMs. Fixing the PRNG seed is essential for testing deterministic uniqueness. Varying the seed is necessary for assessing stochastic consistency [7]. |
| LHS-PRCC Analysis [7] | Parameter sweep and sensitivity analysis. | A technique combining Latin Hypercube Sampling (LHS) with Partial Rank Correlation Coefficient (PRCC) to assess the influence of input parameters on outputs, crucial for identifying ill-conditioning. |
| ASME V&V 40 Standard [5] | Regulatory credibility framework. | A technical standard for assessing the credibility of computational models, providing a risk-informed framework for planning verification and validation activities for regulatory submission. |
| High-Fidelity Field Data [15] | Multi-level validation. | Real-world data used not only for overall model validation but also to validate the behavior of individual agents and their interactions, ensuring the model's emergent dynamics are realistic. |
Integrating Existence and Uniqueness within the Broader VV&UQ Framework
This technical support center provides troubleshooting guides and FAQs for researchers, scientists, and drug development professionals conducting verification, validation, and uncertainty quantification (VV&UQ) for Agent-Based Models (ABMs), with a specific focus on existence and uniqueness analysis.
# Frequently Asked Questions (FAQs)
1. What are existence and uniqueness analysis, and why are they critical first steps in ABM verification?
Existence and uniqueness analysis are fundamental components of the deterministic verification of an ABM. They ensure the model's numerical and computational robustness before more complex validation.
- Existence Analysis: This procedure verifies that the computational model produces an output for every reasonable input value within the defined parameter space. It checks that the simulation runs to completion without fatal errors across its intended operating range [7].
- Uniqueness Analysis: This test ensures that for an identical set of inputs (including the same random seed), the model produces the same outputs across different simulation runs, with at most minimal variations due to numerical rounding errors inherent to computing platforms. A failure of uniqueness suggests underlying instabilities or implementation errors in the code [7].
These analyses form the foundation of model credibility, especially for in-silico trials intended for regulatory evaluation of medicinal products. A model that fails these tests cannot be considered reliable for generating evidence on drug safeness or efficacy [7].
2. Within the broader VV&UQ workflow, when should I perform existence and uniqueness analysis?
Existence and uniqueness analysis are not isolated activities; they are initial, critical steps within a larger, iterative verification workflow. A typical structured approach includes [7]:
- Deterministic Verification:
- Existence and Uniqueness Analysis
- Time Step Convergence Analysis: Ensures the model's outputs are not overly sensitive to the discrete time-step length chosen for the simulation.
- Smoothness Analysis: Checks for unnatural singularities or discontinuities in output time series that may indicate numerical errors.
- Parameter Sweep Analysis: Tests the model across its input parameter space to identify regions of ill-conditioning or abnormal sensitivity.
- Stochastic Verification (for subsequent steps):
- Consistency and Sample Size analysis to ensure the number of stochastic runs is sufficient.
3. My ABM is inherently stochastic. How can I test for uniqueness when outputs are supposed to vary?
This is a common point of confusion. The uniqueness test is part of deterministic verification. To perform it, you must temporarily remove the primary sources of stochasticity. This is typically done by initializing the model's pseudo-random number generator with a fixed seed. When the same initial seed is used, the sequence of "random" numbers is identical, and thus all model outputs should also be identical. A failure to produce identical outputs under a fixed seed indicates a non-determinism bug in the code, such as reliance on an unseeded system clock or uninitialized variables [7].
4. What are the most common root causes for uniqueness failures in an ABM?
Failures in uniqueness analysis often stem from implementation errors that introduce unintended non-determinism.
- Uncontrolled Random Number Generators: Using a random number generator that is not properly seeded or reseeded at the start of each run.
- Parallel Processing Race Conditions: In parallelized code, where multiple processing threads access and modify shared data or resources simultaneously without proper synchronization, leading to unpredictable execution orders.
- Floating-Point Non-Associativity: The order of arithmetic operations (especially addition) on floating-point numbers can yield slightly different results due to rounding. This can be triggered by non-deterministic thread execution orders.
- External Data or Timing Dependencies: The model relying on external data sources, system timestamps, or user input that may change between runs.
# Troubleshooting Guides
# Problem: Model Fails Uniqueness Test (Outputs Diverge with Fixed Seed)
Symptoms: When running the ABM multiple times with an identical input parameter set and a fixed random seed, the output trajectories or final results are not identical.
Diagnosis and Resolution Table:
| Symptom | Potential Root Cause | Recommended Solution |
|---|---|---|
| Slight numerical differences in outputs (e.g., at the 10th decimal place). | Expected numerical rounding errors from different operation orders on floating-point numbers. | Verify that the differences are within a defined tolerance level (e.g., eqi < 5%) [7]. This may not be a critical failure. |
| Significant divergence in outputs from the first few time steps. | Unseeded or incorrectly seeded random number generator. | Implement a fixed seed for the model's primary and all secondary random number generators at the start of every simulation run. |
| Divergence occurs only when the model runs on multiple CPU cores. | Race condition in parallelized code. | Use debugging tools to identify shared resources. Implement mutex locks, semaphores, or redesign the algorithm to avoid shared state. |
| Outputs are "mostly" the same but show sporadic, unexpected jumps. | Reliance on system time or external input. | Refactor the code to remove dependencies on the system clock or external files for core model logic. Use the fixed random seed for all stochastic decisions. |
# Problem: Model Fails Existence Test (Crashes or Hangs)
Symptoms: The ABM fails to complete a simulation run, resulting in a crash, hang, or fatal error for certain input parameter values.
Diagnosis and Resolution Table:
| Symptom | Potential Root Cause | Recommended Solution |
|---|---|---|
| Crash occurs when accessing an array or list index. | Invalid agent state or out-of-bounds world interaction. The model attempts an operation that is not defined. | Add comprehensive input validation and state checks. Implement try-catch blocks to log the precise state of the model at the point of failure. |
| Simulation hangs indefinitely, often in a loop. | Violation of a model assumption leading to an infinite loop or deadlock (e.g., an agent cannot find a valid move). | Introduce loop counters with hard limits. Add detailed logging to identify the agent and its state when the hang occurs. Check agent decision logic for exit conditions. |
| Crash occurs for specific parameter combinations during a parameter sweep. | Numerical ill-conditioning, such as division by zero or arithmetic overflow, for extreme parameter values [7]. | Perform Parameter Sweep Analysis to map the "valid" and "invalid" regions of your input parameter space. Introduce safeguards (e.g., clipping extreme values) or redefine the model's domain to exclude non-physical parameter combinations. |
| The model runs but produces nonsensical outputs (e.g., negative population counts). | Logical error in agent rules or world dynamics that violates a fundamental constraint. | This is a verification failure. Implement "sanity check" rules for agent behaviors and environment updates to ensure they adhere to physical or logical constraints (e.g., population counts cannot go negative). |
# Experimental Protocol: A Step-by-Step Guide for Existence and Uniqueness Analysis
This protocol provides a detailed methodology for conducting existence and uniqueness analysis, as adapted from the verification workflow for mechanistic ABMs [7].
Objective: To verify that the ABM produces a valid output for all intended inputs (existence) and that this output is reproducible for identical inputs (uniqueness).
Materials and Computational Tools:
- The ABM software and its runtime environment.
- A computing cluster or machine capable of running multiple model instances.
- (Recommended) Automated scripting to manage multiple runs (e.g., Python, Bash).
- (Recommended) Model Verification Tools (MVT) or similar frameworks for automating verification tests [7].
Procedure:
Part A: Existence Analysis
- Define the Input Parameter Space: Identify all input parameters for the model and define their plausible ranges based on theoretical or empirical grounds.
- Design a Sampling Strategy: Use a space-filling design like Latin Hypercube Sampling (LHS) to efficiently sample the multi-dimensional parameter space. This ensures broad coverage without the combinatorial explosion of a full factorial design [7].
- Execute Batch Runs: For each sampled parameter set, execute the model.
- Monitor for Failures: Record whether each run (a) completes successfully, (b) crashes, or (c) hangs.
- Analyze and Map Results: Identify regions in the parameter space where the model fails to run. Investigate and correct the root causes of these failures, as they indicate a violation of the model's "existence" condition.
Part B: Uniqueness Analysis
- Select Representative Parameter Sets: Choose a subset of parameter sets from Part A that led to successful model execution.
- Initialize with a Fixed Seed: For each selected parameter set, configure the model to use a single, fixed seed for its random number generator.
- Execute Replicated Runs: Run the model multiple times (e.g., 5-10 times) for each parameter set, using the same fixed seed every time.
- Compare Outputs: For each set of replicated runs, compare the key output variables. Use a tolerance-based comparison (e.g.,
eqi < 5%[7]) to account for negligible floating-point differences. - Identify Non-Uniqueness: If outputs for identical input-seed pairs are not consistent, use the troubleshooting guide above to diagnose the source of non-determinism in the code.
# Research Reagent Solutions: Essential Tools for ABM Verification
The following table details key computational tools and methodologies essential for conducting rigorous existence and uniqueness analysis and broader VV&UQ.
| Tool / Method | Function in Verification | Relevance to Existence/Uniqueness |
|---|---|---|
| Model Verification Tools (MVT) | An open-source software suite that automates key steps in the deterministic verification of discrete-time models, including ABMs [7]. | Provides a structured framework and automated procedures for running the parameter sweeps and replicated runs needed for existence and uniqueness testing. |
| Latin Hypercube Sampling (LHS) | A statistical method for generating a near-random sample of parameter values from a multidimensional distribution. It is efficient for exploring high-dimensional parameter spaces [7]. | Core to Existence Analysis. Used to systematically sample the input parameter space to test for model crashes or hangs. |
| Fixed Increment Time Advance (FITA) | The most common time-advance mechanism in ABMs, which progresses the simulation in discrete, fixed-time steps [7]. | The choice of time-step can indirectly affect uniqueness if it influences operation order. It is the subject of a separate Time Step Convergence Analysis. |
| Pseudo-Random Number Generator (PRNG) | An algorithm that generates a sequence of numbers that approximates the properties of random numbers. It can be initialized with a 'seed' [7]. | Critical for Uniqueness Analysis. Using a fixed, reproducible seed is the primary method for isolating and testing the model's deterministic core. |
| Parameter Sweep Analysis | A technique that involves running the model multiple times while systematically varying input parameters to assess the model's response [7]. | The primary methodology for conducting a comprehensive Existence Analysis to find regions of failure in the input space. |
| Sobol Sensitivity / LHS-PRCC | Variance-based and correlation-based sensitivity analysis techniques used to quantify how input uncertainty contributes to output uncertainty [7]. | While more common in later validation/UQ stages, these can help identify parameters that most influence model instability discovered during existence testing. |
A Practical Framework for Implementing Existence and Uniqueness Analysis
Before an Agent-Based Model (ABM) can be used for mission-critical applications, such as predicting the efficacy of a new drug in in silico trials, its credibility must be rigorously assessed. Deterministic verification is a fundamental part of this process, aiming to identify, quantify, and reduce the numerical errors associated with the model itself [17]. For ABMs, which often simulate complex, emergent behaviors from the bottom up, this presents a unique challenge. Unlike equation-based models where numerical error can be assessed against an analytical solution, the "local rules" of an ABM require a specialized verification framework [17] [7].
This guide, framed within broader research on existence and uniqueness analysis, provides a practical workflow to help researchers and scientists ensure their computational models are robust and numerically sound. A verified model is a reliable model, and in the context of drug development, this reliability is paramount for regulatory acceptance [7].
Frequently Asked Questions
Q: Why is deterministic verification separate from stochastic verification? A: Many ABMs use Pseudo-Random Number Generators (PRNGs) to simulate uncertainty. Deterministic verification involves running the model with a fixed random seed, ensuring that any variation in output is due to numerical approximation and not the model's inherent randomness. This isolation allows you to pinpoint numerical errors [17] [7].
Q: How does this relate to "existence and uniqueness" in my ABM? A: In mathematical modeling, existence and uniqueness theorems guarantee that a solution exists and is unique for a given set of inputs. In computational ABM verification, we adapt this concept. We check that the model produces a solution for all reasonable inputs (existence) and that, for the same fixed inputs and random seed, it produces the same solution every time, within a small tolerance defined by numerical precision (uniqueness) [7] [18].
Q: My ABM results are stochastic by nature. Is deterministic verification still relevant? A: Absolutely. Before you can trust the statistical distributions of your stochastic results, you must first verify that the underlying deterministic logic of your agent interactions and state changes is implemented correctly and consistently. Deterministic verification is the first step in establishing this trust [17].
The Deterministic Verification Workflow: A Step-by-Step Guide
The following workflow, synthesized from established verification procedures, is designed to be implemented systematically on your ABM [17] [7].
Step 1: Existence and Uniqueness Analysis
Objective: To verify that the model produces a valid output for a given input and that this output is reproducible.
Experimental Protocol:
- Define Input Space: Identify the key input parameters for your model. For a biological ABM, this could include initial agent counts, environmental factors, or kinetic parameters.
- Test for Existence: Sample across the admissible range of your input parameters. For each input set, run the model and verify that it completes without fatal errors and produces a logically valid output.
- Test for Uniqueness: Select a representative subset of input parameter sets. Run the model multiple times (e.g., 10-20 runs) for each input set using the same fixed random seed. The output across these repeated runs should be identical, with at most minimal variations due to floating-point rounding errors [7].
Troubleshooting Guide:
- Problem: The model crashes for specific input values.
- Solution: Identify the root cause, often a division by zero, an out-of-bounds array access, or an invalid state transition. Implement safeguards or correct the model logic.
- Problem: The model runs but produces different results for the same input and random seed.
- Solution: This indicates a violation of uniqueness, often caused by parallel processing race conditions, the use of non-fixed random seeds in parts of the code, or uninitialized variables. Review your code for these issues.
Step 2: Time Step Convergence Analysis
Objective: To ensure that the discrete-time approximation used in the simulation does not unduly influence the results.
Experimental Protocol:
- Select a Reference Output: Choose a key quantitative output from your model (e.g., final agent count, peak value of a critical variable, or mean value over time).
- Run with Decreasing Time Steps: Execute the model with a series of progressively smaller time steps (e.g.,
dt,dt/2,dt/4), keeping the random seed fixed. - Calculate Discretization Error: For each run, calculate the percentage error of your output quantity relative to the result from the smallest, computationally feasible time step (your reference solution,
i*). The formula is: ( e_{q}^{i} = \frac{{q^{i} - q^{i} }}{{q^{i} }} \times 100 ) where ( q^{i*} ) is the reference output and ( q^{i} ) is the output at time-stepi[7]. - Check for Convergence: The model is considered converged when the error ( e_{q}^{i} ) falls below a pre-defined tolerance (e.g., 5%).
Troubleshooting Guide:
- Problem: The discretization error does not decrease with a smaller time step.
- Solution: This may suggest an instability in the model's algorithm or a bug in the implementation of time-advancement logic. Review the model's core interaction and update functions.
Step 3: Smoothness Analysis
Objective: To identify unintended numerical stiffness, singularities, or discontinuities in the model output over time.
Experimental Protocol:
- Generate Output Time Series: Run the model and record a key output variable over time.
- Calculate the Coefficient of Variation (D): For the output time series, calculate the standard deviation of the first difference, scaled by the absolute mean of these differences. This is often done using a moving window (e.g., k=3 neighbors) to analyze local variation.
- Interpret the Results: A high value of
Dindicates a "bumpy" or discontinuous output, which may be a sign of numerical instability or unintended model behavior that requires investigation [7].
Step 4: Parameter Sweep Analysis
Objective: To ensure the model is not ill-conditioned, meaning it does not exhibit extreme sensitivity to tiny changes in inputs.
Experimental Protocol:
- Design the Sweep: Use sampling methods like Latin Hypercube Sampling (LHS) to efficiently explore the multi-dimensional input parameter space.
- Run the Ensemble: Execute the model for each sampled parameter set.
- Analyze Sensitivity and Validity: Check for input regions where the model fails or produces outputs outside expected biological or logical bounds. Use sensitivity analysis techniques, such as calculating Partial Rank Correlation Coefficients (PRCC), to quantify how much each input parameter influences the output. A model is ill-conditioned if a small parameter change causes a disproportionately large output shift [7].
The workflow for deterministic verification can be visualized as a sequential process where the output of one step informs the next, as shown in the following diagram:
Quantitative Criteria for Verification Success
The table below summarizes the key metrics and their success criteria for the deterministic verification workflow.
Table 1: Key Metrics for Deterministic Verification Steps
| Verification Step | Primary Metric | Success Criteria | Common Tools & Methods |
|---|---|---|---|
| Existence & Uniqueness | Output variability over repeated runs (fixed seed) | Zero variability (bit-wise identical outputs) or variation within floating-point error tolerance [7]. | Custom scripts, Unit tests |
| Time Step Convergence | Percentage discretization error (( e_{q}^{i} )) | Error below a set tolerance (e.g., < 5%) when compared to a reference solution with a finer time step [7]. | Model Verification Tools (MVT) [7] |
| Smoothness Analysis | Coefficient of Variation (D) | A low value of D, indicating a smooth output trajectory without abnormal buckling or discontinuities [7]. | Model Verification Tools (MVT) [7] |
| Parameter Sweep | Partial Rank Correlation Coefficient (PRCC) | No extreme, non-monotonic sensitivity; model outputs remain within valid bounds across the input space [7]. | LHS Sampling, PRCC Analysis, SALib [7] |
The Scientist's Toolkit: Essential Research Reagent Solutions
In computational science, "research reagents" refer to the software tools and libraries that enable verification. The following table lists key resources for implementing the workflow described above.
Table 2: Essential Computational Tools for ABM Verification
| Tool / Resource | Type | Primary Function in Verification |
|---|---|---|
| Model Verification Tools (MVT) [7] | Software Platform | An open-source toolkit that automates key steps like time step convergence and smoothness analysis. Essential for a standardized approach. |
| SALib [7] | Python Library | Provides robust algorithms for sensitivity analysis, including Sobol and Morris methods, crucial for parameter sweep analysis. |
| Pingouin & Scikit-learn [7] | Python Libraries | Used for statistical analysis, including calculating Partial Rank Correlation Coefficients (LHS-PRCC) for parameter sensitivity. |
| Latin Hypercube Sampling (LHS) | Methodology | An efficient statistical method for exploring the parameter space of a model with a limited number of runs [7]. |
| Fixed Increment Time Advance (FITA) | Core Algorithm | The standard time-advancement method in most ABM frameworks. Its configuration is the target of time step convergence analysis [7]. |
A rigorous, step-by-step deterministic verification workflow is not merely an academic exercise but a foundational practice for any researcher employing Agent-Based Models in high-stakes environments like drug development. By systematically confirming that your model produces unique and reproducible results, converges with appropriate time steps, produces smooth outputs, and responds reasonably to parameter changes, you build a bedrock of credibility upon which further validation and experimentation can safely rest.
Frequently Asked Questions (FAQs)
Q1: What is the primary purpose of the Mobile Verification Toolkit (MVT)? MVT is designed to facilitate the consensual forensic analysis of Android and iOS devices to identify traces of compromise [19] [20]. It helps in conducting forensics of mobile devices to find signs of a potential compromise [21].
Q2: Is MVT suitable for non-technical users to perform self-assessments? No. MVT is a forensic research tool intended for technologists and investigators. Using it requires an understanding of forensic analysis and command-line tools. It is not intended for end-user self-assessment [20].
Q3: Can MVT guarantee that a device is free of spyware? No. Public Indicators of Compromise (IOCs) alone are insufficient to determine that a device is "clean". Reliance on them can miss recent forensic traces and provide a false sense of security. Comprehensive analysis often requires access to non-public IOCs and threat intelligence [20].
Q4: What are the key capabilities of MVT? Key features include decrypting iOS backups, parsing records from iOS system and app databases, extracting apps from Android devices, comparing records against malicious IOCs, and generating JSON logs and chronological timelines of records [20].
Q5: Is it permissible to use MVT on devices without the user's consent? No. The use of MVT to extract or analyze data from devices of non-consenting individuals is explicitly prohibited by its license [20].
Troubleshooting Guides
Issue 1: Incomplete or Failed Data Acquisition from an Android Device
Problem: The mvt-android command fails to extract a complete set of installed applications or diagnostic information.
Solution:
- Verify USB Debugging: Ensure that USB debugging is enabled on the Android device within the "Developer options" menu.
- Check Device Connection: Use the
adb devicescommand to confirm your computer recognizes the device and that you have authorized the connection. - Review Permissions: Some information may require root access to extract. Note that MVT is designed for consensual forensics, and rooting a device may not always be feasible or desired [20].
- Re-run with Detailed Logging: Execute the command with the
-v(verbose) flag to generate more detailed output, which can help pinpoint the stage at which the failure occurs.
Issue 2: Processing Encrypted iOS Backups
Problem: MVT is unable to decrypt an encrypted iOS backup.
Solution:
- Confirm Password: Ensure you have the correct backup password. MVT will prompt you for this password during the decryption process [20].
- Verify Backup Integrity: Confirm that the backup file is not corrupted. Try creating a new backup via iTunes or Finder.
- Use Latest MVT Version: Update to the latest version of MVT, as decryption capabilities are continuously improved [19].
Issue 3: Interpretation of IOC Scan Results
Problem: The tool outputs a list of potential malicious traces, but the significance is unclear.
Solution:
- Review IOC Source: Check the origin and date of the Indicator of Compromise file you are using. Older IOCs may not detect recent threats [20].
- Examine the JSON Logs: Generate and carefully review the detailed JSON logs of detected traces for additional context [20].
- Seek Expert Consultation: For reliable triage, seek support from organizations like Amnesty International's Security Lab or Access Now’s Digital Security Helpline, which have access to non-public research and intelligence [20].
The Scientist's Toolkit: Research Reagent Solutions
The following table details key digital "reagents" and materials used in mobile forensic analysis with MVT.
| Research Reagent / Material | Function in Analysis |
|---|---|
| iOS Backup Image | A forensic copy of the device's file system and application data. Serves as the primary source for parsing records and logs [20]. |
| Android ADB Extraction | Diagnostic information and a list of installed applications extracted from an Android device via the Android Debug Bridge (adb) protocol [20]. |
| Indicators of Compromise (IOCs) - STIX2 Format | A standardized list of known malicious patterns (e.g., file hashes, domains). Used by MVT to scan device data and identify potential threats [20]. |
| Chronological Timeline | A unified timeline of system events generated by MVT. Allows the researcher to analyze the sequence and correlation of activities on the device [20]. |
| JSON Logs of Records | Structured logs of all extracted records from the device. Facilitates detailed manual review and automated processing of the data [20]. |
Experimental Protocols
Protocol 1: Forensic Acquisition of an iOS Device via Backup
Objective: To create a verifiable data image of an iOS device for subsequent forensic analysis.
Methodology:
- Create a Local Backup: Connect the iOS device to a trusted computer and use iTunes (on Windows) or Finder (on macOS) to create an encrypted local backup. Encryption is required to extract the most comprehensive data set.
- Verify Backup Completion: Ensure the backup process completes successfully without errors.
- Transfer Backup for Analysis: Locate the backup folder on the computer system. The path is typically:
- macOS:
~/Library/Application Support/MobileSync/Backup/ - Windows:
\Users\(username)\AppData\Roaming\Apple Computer\MobileSync\Backup\
- macOS:
- Acquire with MVT: Use the
mvt-ioscommand-line tool, pointing it to the location of the backup folder and providing the backup password for decryption [20].
Protocol 2: Indicator of Compromise (IOC) Scanning and Validation
Objective: To systematically scan acquired device data for known malicious indicators and validate the findings.
Methodology:
- IOC Sourcing: Obtain a current, reputable set of IOCs in the STIX2 format. This could be from public research reports or trusted threat intelligence feeds [20].
- Execute MVT Scan: Run the appropriate MVT command (e.g.,
mvt-ios check-backupormvt-android check-iocs) specifying the path to the acquired data and the IOC file[s]. - Result Triage: MVT will generate two primary outputs [20]:
- A full JSON log of all extracted records.
- A separate JSON log of all detected malicious traces.
- Expert Analysis: Correlate the detected traces within the generated chronological timeline. Context is critical; a single match may not confirm a compromise, while a cluster of related IOCs is more significant. False positives must be ruled out [20].
Workflow Visualization
MVT Forensic Analysis Workflow
IOC Validation & Triage Logic
Troubleshooting Guide: Common UISS Platform Issues
Issue 1: Poor Visual Contrast in Simulation Outputs
Problem: Visualization outputs from the UISS platform lack sufficient contrast, making it difficult to distinguish between different agent types or states, especially in the simulated tissue environment [22].
Solution: Implement automated contrast checking.
- For Programmatic Generation: Calculate the luminance of the background color and set the text or agent color accordingly. Use the formula:
label_col <- ifelse(hcl[, "l"] > 50, "black", "white")to ensure text is readable [23]. - For Manual Design: Adhere to WCAG 2.1 (Level AA) standards, which require a minimum 3:1 contrast ratio for meaningful graphics and large text [22]. Use online contrast checker tools to validate your color pairs.
Issue 2: Ineffective or Misleading Color Palettes
Problem: The chosen color palette for categorical data (e.g., different cell phenotypes) creates false associations or is not differentiable by users with color vision deficiencies [22].
Solution: Utilize a pre-validated, accessible categorical palette.
- Selection: Choose palettes that are both differentiated (sufficient visual contrast between colors) and diverse (avoid false correlations due to similar hues or brightness) [22].
- Validation: Use tools like Viz Palette to evaluate the palette's effectiveness. This tool generates reports on the "just-noticeable difference" (JND) between colors, helping to identify hues that are hard to tell apart [22].
- Fallbacks: Incorporate secondary accessibility cues like textures, shapes, or patterns to encode information, ensuring robustness against color vision deficiencies [22].
Issue 3: Graphviz Node Rendering Issue
Problem: When generating pathway diagrams using Graphviz DOT language, node fillcolor does not appear in the output.
Solution: Ensure the style=filled attribute is included for the node. The fillcolor attribute only takes effect when a fill style is applied [24].
Frequently Asked Questions (FAQs)
FAQ 1: What are the core principles for designing cognitively efficient ABM visualizations? Effective ABM visualizations should facilitate swift perceptual inferences. Key principles derived from Gestalt psychology and scientific visualization include [25]:
- Foreground/Background Segregation: Clearly distinguish agents from their environment.
- Informed Use of Visual Variables: Use variables like color, size, and shape in ways that match the data type (e.g., hue for categorical data).
- Removal of Visual Interference: Eliminate unnecessary visual elements that do not contribute to the model's message. The primary goals are to simplify, emphasize, and explain the model's key behaviors [25].
FAQ 2: How does the UISS platform handle the specific recognition between immune cells and pathogens? The UISS platform uses an abstraction based on binary strings to mimic the adaptive immune response. Epitopes on pathogens and receptors on immune system cells are both represented by binary strings. The probability of an immune cell recognizing a pathogen is proportional to the Hamming distance (the number of mismatching bits) between their respective strings. This approach efficiently reproduces features like immune memory, specificity, and tolerance [26].
FAQ 3: Why is deriving a mean-field limit important for a hybrid PDE-ABM in mathematical oncology? Deriving a mean-field limit is crucial for connecting stochastic microdynamics to deterministic macrodynamics. It integrates the complex hybrid PDE-ABM system into a single, analytically tractable PDE system. This allows researchers to [27] [28]:
- Rigorously link stochastic agent rules to continuum-scale descriptions.
- Perform formal mathematical analysis (e.g., well-posedness, stability) on the entire system.
- Develop more efficient hybrid numerical schemes that can use the PDE surrogate in non-critical regions, reducing computational cost.
Experimental Protocol: UISS In Silico Vaccine Trial
This protocol outlines the methodology for using the Universal Immune System Simulator (UISS) to predict the efficacy of a candidate vaccine or monoclonal antibody therapy against SARS-CoV-2 [26].
Objective Definition and Conceptual Mapping
- Define the Candidate: Specify the therapeutic agent (e.g., a monoclonal antibody like the one proposed by Wang et al. that targets a communal conserved epitope on the spike receptor binding domain) [26].
- Develop a Conceptual Map: Aggregate existing knowledge and hypotheses about SARS-CoV-2 dynamics and the host immune response into a flow chart. This map should detail the cascade of biological events from infection to immune clearance [26].
Model Formulation and Computational Translation
- Agent and State Definition: Define the agents (e.g., SARS-CoV-2 virions, B cells, T cells, antibodies) and their possible states (e.g., naive, activated, memory) [26].
- Rule Specification: Codify the rules of interaction between agents. This includes:
- Integration of Continuum Fields (for hybrid models): If modeling diffusive substances (e.g., cytokines, oxygen), couple agent-based rules with reaction-diffusion equations (PDEs) to describe their spatial dynamics [27] [28].
Simulation Execution and In Silico Trial
- Calibrate Parameters: Use known biological data (e.g., viral load peaks in the first week, IgG/IgM antibody rise around day 10) to calibrate model parameters [26].
- Run Virtual Cohorts: Execute the model multiple times with a virtual population to account for stochasticity. This constitutes the "in silico trial" [26].
- Administer Virtual Intervention: Introduce the candidate vaccine or monoclonal antibody into the simulation according to the proposed treatment schedule [26].
Output Analysis and Efficacy Prediction
- Monitor Key Metrics: Track simulation outputs such as:
- Time to viral clearance.
- Peak viral load.
- Magnitude and duration of humoral (antibody) and cellular immune responses.
- Incidence of severe symptoms (modeled via cytokine storm markers like IL-6) [26].
- Compare to Control: Compare these metrics against a control cohort that did not receive the virtual intervention.
- Predict Efficacy: The platform predicts the therapy's efficacy based on its ability to significantly improve key metrics (e.g., reduce viral load, accelerate clearance) compared to the control [26].
Diagram: UISS In Silico Trial Workflow
The Scientist's Toolkit: Research Reagent Solutions
Table: Key Components for a Hybrid ABM-PDE Framework in Immunology/Oncology
| Research Reagent / Component | Function & Explanation |
|---|---|
| Agent-Based Model (ABM) | Core simulation engine for modeling discrete, stochastic entities (e.g., individual immune cells, tumor cells, vessel agents) and their rule-based interactions [26] [25]. |
| Partial Differential Equations (PDEs) | Describes the spatiotemporal dynamics of continuum fields (e.g., concentration gradients of oxygen, cytokines, drugs) within the tissue microenvironment [27] [28]. |
| Gillespie Algorithm | An exact stochastic simulation algorithm (a Monte Carlo method) used to model the timing and occurrence of random events, such as phenotypic switching in tumor cells or stochastic mutation events [27] [28]. |
| Mean-Field Limit Derivation | A mathematical technique (using moment-closure) to derive a deterministic PDE description from the stochastic ABM rules. This connects micro-scale randomness to macro-scale dynamics and aids in analysis [27] [28]. |
| Binary String Recognition | A computational method used in UISS to abstractly mimic the specific binding between immune cell receptors and pathogen epitopes, enabling simulation of adaptive immunity [26]. |
| Visualization & Gestalt Principles | Guidelines for creating cognitively efficient visualizations of ABM outputs, ensuring emergent behaviors and key model features are clearly communicated [25]. |
Diagram: Simplified Signaling in the Tumor Microenvironment
Troubleshooting Guides & FAQs
Frequently Asked Questions
Q1: What does a "No fixed point found" error mean for the validity of my Agent-Based Model? A "No fixed point found" error indicates that, within the defined mathematical framework, your ABM lacks a verifiable equilibrium state. This does not necessarily invalidate your model but suggests it may represent a system that is inherently unstable, oscillatory, or chaotic. You should first verify the correctness of your translation from the ABM to the mathematical equation system. If correct, this result can be a significant finding about the system's dynamics, but it means techniques relying on equilibrium analysis are not applicable.
Q2: My model's state space is vast and high-dimensional. How can I make fixed-point analysis computationally feasible? High dimensionality is a common challenge. Apply dimensionality reduction techniques like Principal Component Analysis (PCA) on sampled model states to identify a lower-dimensional manifold in which the system's essential dynamics occur. You can then search for fixed points within this reduced space. Furthermore, consider applying fixed-point theorems on simpler, abstracted versions of your model that capture its core interactions before scaling up to the full complexity.
Q3: How do I handle non-continuous agent behaviors when applying Brouwer's theorem, which requires continuity? Brouwer's Fixed-Point Theorem indeed requires a continuous mapping on a convex, compact set. If agent behaviors are discrete or non-continuous, you have two primary paths:
- Smoothing: Replace discrete rules (e.g., step functions) with continuous, sigmoidal approximations. This creates a continuous model amenable to analysis, and you can study the convergence back to the discrete case.
- Alternative Formulation: Use the Kakutani Fixed-Point Theorem, which generalizes Brouwer's theorem to set-valued functions (correspondences) and can directly handle certain types of discontinuities and discrete choices.
Q4: What does it mean if my analysis finds multiple fixed points? Finding multiple fixed points is a critical insight. It means your ABM is multistable; depending on the initial conditions, the system can evolve to one of several distinct equilibrium states. For drug development, this could theoretically represent different disease outcomes (e.g., remission vs. chronic state). You must characterize the basin of attraction for each fixed point—the set of initial conditions that lead to each equilibrium—to understand the model's long-term behavior.
Q5: How can I verify that a discovered fixed point is unique for my specific ABM? Proving uniqueness is often more challenging than proving existence. Strategies include:
- Contractive Mapping: Show that your model's state transition function is a contraction. If the function is Lipschitz continuous with a constant less than 1, Banach's Fixed-Point Theorem guarantees a unique fixed point.
- Jacobian Analysis: Analyze the Jacobian matrix of the system's dynamics at the fixed point. Specific spectral properties can indicate local uniqueness.
- Index Theory: In more complex cases, fixed-point index theory can be used to rule out the existence of additional fixed points within a defined region.
Common Experimental Errors & Resolutions
| Error Message / Symptom | Likely Cause | Resolution Protocol |
|---|---|---|
| "Iteration limit exceeded without convergence." | The chosen numerical method (e.g., Newton-Raphson) is failing to find a fixed point within the allowed steps. | 1. Check the Lipschitz constant of your mapping; it may be too close to or exceed 1. 2. Switch to a more robust root-finding algorithm (e.g., Levenberg-Marquardt). 3. Verify the convexity and compactness of your defined state space. |
| "Solution violates model constraints." | The mathematical solver has found a fixed point, but it lies outside biologically or physically plausible ranges (e.g., negative cell counts). | 1. Reformulate your problem to explicitly include constraints (e.g., use Lagrange multipliers). 2. Re-define the state space to be a closed and bounded (compact) set that inherently respects the constraints (e.g., population fractions between 0 and 1). |
| High sensitivity to initial parameter values. | The model's dynamics are highly nonlinear, and the fixed-point landscape may have a very small basin of attraction for some equilibria. | 1. Perform a global sensitivity analysis (e.g., Sobol method) to identify the most influential parameters. 2. Conduct a extensive parameter sweep to map out the different basins of attraction and their boundaries (bifurcation analysis). |
| Fixed point is found but is unstable. | The equilibrium exists but is not robust to small perturbations. This is common in models representing transition states or pathological thresholds. | Analyze the eigenvalues of the Jacobian matrix at the fixed point. An unstable point will have at least one eigenvalue with a positive real part. In a therapeutic context, this could represent a drug target to push the system away from this state. |
The Scientist's Toolkit: Research Reagent Solutions
| Reagent / Tool | Function in ABM Verification |
|---|---|
| Banach Fixed-Point Theorem | Provides a constructive method for finding a unique fixed point by proving the model's state-transition function is a contraction mapping, guaranteeing convergence from any initial condition. |
| Brouwer Fixed-Point Theorem | Used to prove the existence of at least one equilibrium point in continuous models defined on convex, compact sets, even when the exact point cannot be easily computed. |
| Kakutani Fixed-Point Theorem | Essential for extending existence proofs to ABMs with set-valued dynamics or discrete choices, generalizing Brouwer's theorem for correspondences. |
| Newton-Raphson Method | A powerful numerical algorithm for rapidly converging to a fixed point when a good initial guess is available and the function is well-behaved. |
| Lipschitz Constant Analysis | Quantifies the sensitivity and stability of the model. A constant less than 1 is required for the Contractive Mapping Theorem, ensuring model predictability. |
| Jacobian Matrix | The key tool for local stability analysis of a discovered fixed point. Its eigenvalues determine whether the equilibrium is a stable attractor or an unstable repeller. |
| Phase Portrait Visualization | A graphical technique for visualizing the dynamics of a system in a reduced state space, allowing researchers to identify fixed points, limit cycles, and basins of attraction. |
Experimental Protocol: Verifying Equilibrium Existence in a Pharmacokinetic-Pharmacodynamic ABM
Objective: To formally verify the existence of a steady-state (equilibrium) in an ABM simulating drug concentration and target engagement.
Methodology:
System Abstraction:
- Let the ABM's state at time ( t ) be represented by a vector ( St = (Ct, Rt, Et) ), where:
- ( Ct ): Average plasma drug concentration across all agent-based compartments.
- ( Rt ): Fraction of target receptors occupied.
- ( E_t ): Measured physiological effect.
- Run multiple simulation batches from varied initial conditions to observe the macroscopic dynamics and define the state space ( \Omega ).
- Let the ABM's state at time ( t ) be represented by a vector ( St = (Ct, Rt, Et) ), where:
Mapping Definition:
- Define a mapping ( T: \Omega \to \Omega ) such that ( T(St) = S{t+\Delta t} ), where ( S_{t+\Delta t} ) is the state vector after a sufficiently long simulation time step ( \Delta t ) that allows for agent interactions to propagate.
Applying Fixed-Point Theorems:
- Step 1: Establish Compactness and Convexity. Show that the state space ( \Omega ) is homeomorphic to a convex, compact subset of ( \mathbb{R}^3 ) (e.g., a cube defined by ( 0 \leq C \leq C{max}, 0 \leq R \leq 1, 0 \leq E \leq E{max} )).
- Step 2: Establish Continuity. Perform a sensitivity analysis on the mapping ( T ). Demonstrate that small changes in ( St ) lead to small changes in ( T(St) ), supporting the assumption of continuity required by Brouwer's theorem.
- Step 3: Invoke Brouwer's Fixed-Point Theorem. Given ( T ) is a continuous mapping from a convex, compact set to itself, conclude that there exists at least one fixed point ( S^* ) such that ( T(S^) = S^ ). This ( S^* ) is the verified equilibrium state of the ABM.
Numerical Validation:
- Use an iterative numerical method (e.g., Newton-Raphson) on the abstracted mapping ( T ) to compute the coordinates of the fixed point ( S^* ).
- Initialize the ABM at the state ( S^* ) and run the simulation to confirm that the macroscopic observables remain stable, validating the mathematical finding.
Workflow & Logical Relationship Diagrams
ABM Verification with Fixed-Point Theorems
Fixed-Point Analysis Decision Tree
Frequently Asked Questions
1. What are existence and uniqueness analysis in the context of ABM verification? In Agent-Based Model (ABM) verification, existence analysis checks that the computational model produces an output value for any given reasonable input parameter range. Uniqueness analysis verifies that identical input sets, including the same random seed, always produce the same outputs, allowing at most for minimal tolerated variation determined by numerical rounding algorithms [7].
2. Why do my model runs with identical seeds produce different results? This is a failure of uniqueness, often caused by:
- Numerical Instability: The model may be ill-conditioned, where tiny floating-point errors are amplified.
- Parallel Processing Race Conditions: If agents are processed in parallel, the order of operations might not be deterministic.
- Uninitialized Variables: Variables not properly reset between simulations can carry over state.
- External Random Number Calls: The model might be accessing a random number generator outside of the controlled, seeded instance.
3. How can I test for solution existence across a wide parameter space? Use a parameter sweep analysis. This involves sampling the entire input parameter space to check if the model fails to produce a valid solution for some input sets or if the solution is valid but outside the expected range. Techniques like Latin Hypercube Sampling (LHS) can efficiently explore high-dimensional parameter spaces [7].
4. My model runs without crashing, but how do I know the solution is truly "correct"? A model not crashing is a basic existence check. To assess correctness, you must define a validity range for your outputs based on theoretical expectations or empirical data. During parameter sweeps, you should flag solutions that, while numerically valid, fall outside this validity range as potential failures of the model's conceptual design [7].
Troubleshooting Guides
Problem: Non-Unique Solutions with Identical Inputs
Symptoms: Running the same model with an identical random seed produces different output trajectories.
Diagnosis and Resolution Protocol:
- Isolate the Random Seed: Ensure the entire simulation, including all agent initialization and behavioral logic, uses a single, controlled pseudo-random number generator (PRNG) that is reset with the same seed at the start of each run [7].
- Check for Parallelism: If your model uses parallel processing, identify if the non-determinism stems from race conditions. Implement a deterministic scheduling algorithm or switch to a sequential execution mode for verification.
- Increase Numerical Precision: Run the model using double-precision (64-bit) floating-point arithmetic instead of single-precision (32-bit) to reduce the impact of round-off errors [7].
- Code Audit: Manually inspect the code for:
- Use of uninitialized variables.
- Calls to system time or other external, non-seeded sources of randomness.
- Complex conditional logic that might be sensitive to minute numerical differences.
Table: Key Research Reagent Solutions for Deterministic Verification
| Reagent / Tool | Function in Verification Process |
|---|---|
| Fixed-Precision Arithmetic Libraries | Enforces consistent numerical representation (e.g., 32-bit vs. 64-bit float) to isolate round-off errors [7]. |
| Deterministic PRNG (e.g., Mersenne Twister) | Provides a reproducible sequence of "random" numbers when initialized with a fixed seed, crucial for testing uniqueness [7]. |
| Unit Testing Framework | Automates the process of running the model multiple times with fixed inputs and seeds to assert output equivalence. |
| Model Verification Tools (MVT) | An open-source suite that provides automated analysis, including uniqueness checks, for discrete-time models [7]. |
Problem: Failure in Solution Existence
Symptoms: The model crashes, hangs, or fails to produce an output for certain parameter combinations during a parameter sweep.
Diagnosis and Resolution Protocol:
- Define Parameter Bounds: Establish physiologically, physically, or theoretically plausible lower and upper bounds for all model parameters.
- Execute a Parameter Sweep: Systematically run the model across the defined parameter space. A structured sampling method like Latin Hypercube Sampling (LHS) is efficient for this purpose [7].
- Log and Categorize Failures: For every failed run, log the exact input parameter set and the nature of the failure (e.g., division by zero, numerical overflow, failure to converge).
- Analyze Failure Clusters: Identify regions in the parameter space where failures cluster. These often point to violations of model assumptions.
- Example: A rule where an agent's growth is a function of
1 / (carrying_capacity - current_population)will fail ifcurrent_population >= carrying_capacity. The existence check would reveal this flawed logic.
- Example: A rule where an agent's growth is a function of
The following workflow diagram outlines the core verification process for an ABM, incorporating both existence and uniqueness analyses.
Problem: Model is Overly Sensitive to Minor Parameter Changes
Symptoms: A tiny change in an input parameter (within plausible bounds) leads to a drastic, discontinuous change in model outputs.
Diagnosis and Resolution Protocol:
- Perform a Local Sensitivity Analysis: Around the parameter value of interest, run a local sweep, varying one parameter at a time and observing the output.
- Calculate Sensitivity Indices: Use global sensitivity analysis methods like Latin Hypercube Sampling-Partial Rank Correlation Coefficient (LHS-PRCC) or Sobol indices to quantify the influence of each input parameter on the output variance [7].
- Identify Ill-Conditioned Parameters: Parameters with very high sensitivity indices may be ill-conditioned. This may require:
- Model Reformulation: Changing the mathematical structure of the model to reduce its sensitivity.
- Better Parameter Estimation: Obtaining more precise empirical estimates for the highly sensitive parameters.
- Theoretical Re-evaluation: Questioning whether the real-world system is truly this sensitive to the factor in question.
Table: Quantitative Error Thresholds for Verification Steps
| Verification Step | Key Metric | Typical Acceptance Threshold | Reference |
|---|---|---|---|
| Time-Step Convergence | Percentage Discretization Error | < 5% | [7] |
| Uniqueness Analysis | Output Variation with Identical Seed | Minimal, bounded by numerical precision | [7] |
| Smoothness Analysis | Coefficient of Variation (D) | Lower is better; indicates less stiffness/buckling | [7] |
The following diagram illustrates a logical decision tree for diagnosing a failure of the Uniqueness test, guiding you to the most probable root cause.
Diagnosing and Resolving Common Pitfalls in ABM Solution Verification
Frequently Asked Questions
Q1: What are the primary empirical red flags indicating a model failure in "existence"? A: A model suffers from "failed existence" when it cannot produce a stable, coherent outcome that corresponds to any observable real-world state. Key red flags include:
- Failure to Converge: The model does not reach a steady state or equilibrium, even after a substantial number of simulation runs, indicating the system dynamics are inherently unstable or mis-specified [9].
- Extreme Outcome Variance: Model outputs show wildly different results across runs with identical parameters, suggesting the system is overly sensitive to stochastic elements rather than its core rules [29].
- Absence of Emergent Phenomena: The model fails to generate the macro-level patterns it was designed to explain, demonstrating a disconnect between the micro-level agent rules and the expected macro behavior [9].
Q2: What symptoms suggest my model has a "non-uniqueness" problem? A: Non-uniqueness occurs when vastly different model configurations or agent behaviors produce functionally identical outputs. This makes it impossible to identify the "true" underlying mechanism. Symptoms are:
- Equifinality: Multiple, divergent sets of initial conditions or parameter values lead to the same final state, preventing you from pinpointing the correct initial setup [9].
- Compensating Parameter Effects: Changes in one parameter can be offset by changes in another, leaving the model output unchanged and making parameter estimation unreliable [9].
- Inability to Invalidate: The model is so flexible that it can be tuned to fit any dataset, which means it does not actually test a specific, falsifiable hypothesis [9].
Q3: What methodologies can I use to test for these issues? A: A rigorous validation protocol is essential. The following table summarizes key experiments and their objectives [29] [9]:
| Experiment Name | Protocol | Key Outcome Measures |
|---|---|---|
| Parameter Sensitivity Analysis | Systematically vary one input parameter at a time across a plausible range while holding others constant. Run the model multiple times for each value. | Sensitivity indices (e.g., Sobol), changes in output distribution, identification of critical parameters that disproportionately drive outcomes. |
| Robustness Check (Stochasticity) | Execute the model numerous times (e.g., 100-1000 runs) with identical parameters but different random number seeds. | Distribution of key outputs (mean, variance, confidence intervals); ensures results are not artifacts of random chance [29]. |
| Historical Data Validation | Initialize the model with past empirical data and run it forward, comparing model-generated outputs to known historical outcomes. | Goodness-of-fit statistics (e.g., RMSE, MAE); visual comparison of trend lines; ability to replicate known emergent patterns [9]. |
The Scientist's Toolkit: Research Reagent Solutions
The following reagents are fundamental for constructing and validating robust agent-based models.
| Reagent / Solution | Function in ABM Verification |
|---|---|
| Synthetic Data Generators | Creates artificial datasets with known properties to test if the model can correctly identify and replicate pre-defined structures and rules. |
| Global Sensitivity Analysis (GSA) Software | Moves beyond one-at-a-time analysis to explore the entire parameter space and discover complex parameter interactions that cause non-uniqueness. |
| Model Profiling & Benchmarking Suites | Tracks computational performance and internal model state changes over time to identify infinite loops, memory leaks, and logic errors. |
| Standardized Experimental Model & Design Frameworks | Provides a structured template for documenting model objectives, entities, rules, and processes, ensuring consistency and reproducibility [29]. |
Diagnostic Workflows for Model Verification
The following diagram outlines a high-level workflow for diagnosing common ABM verification failures.
ABM Verification Diagnosis
Detailed Investigation of Non-Uniqueness
For models suspected of non-uniqueness, a more detailed investigation is required to pinpoint the cause.
Non-Uniqueness Diagnosis
Addressing Numerical Ill-Conditioning through Parameter Sweep Analysis
FAQs and Troubleshooting Guides
Frequently Asked Questions
Q1: What is parameter sweep analysis and why is it crucial for verifying Agent-Based Models (ABMs) in drug development? Parameter sweep analysis is a computational method that involves running a model multiple times while systematically varying key parameters across a defined range to observe changes in outcomes [30]. For ABMs in drug development, this is crucial because it helps researchers understand how sensitive their models are to changes in inputs, identify critical parameters that drive system behavior, test the robustness of findings across different assumptions, and detect numerical ill-conditioning where small parameter changes cause disproportionately large or unexpected shifts in model outputs [31] [32].
Q2: How can I identify if my ABM is suffering from numerical ill-conditioning? Numerical ill-conditioning in ABMs typically manifests as extreme sensitivity to tiny parameter changes, inconsistent or chaotic output patterns from similar initial conditions, failure to converge to stable solutions, or emergence of drastically different macro-level behaviors from minor parameter adjustments [31] [32]. Parameter sweep analysis helps detect these issues by revealing nonlinear responses, threshold effects, and parameter interactions that may indicate underlying instability in the model structure [32].
Q3: What are the best practices for selecting parameters and ranges when designing a sweep analysis for ABM verification? Best practices include prioritizing parameters with uncertain values based on experimental data, using wider ranges initially to explore the parameter space comprehensively, focusing on parameters theorized to influence key outputs, including both parametric and non-parametric elements (e.g., behavioral rules), and employing appropriate sweep types (linear, logarithmic, decade) based on the expected parameter influence [30] [31] [32]. For ABMs specifically, it's important to sweep parameters that operate at both micro (agent) and macro (environmental) levels [31].
Q4: How can I efficiently analyze the large datasets generated from parameter sweeps of complex ABMs? Effective strategies include employing visualization techniques like Individual Conditional Expectation (ICE) plots to track output changes across parameter values, using variance decomposition methods (e.g., Sobol' indices) to quantify each parameter's contribution to output variance, applying statistical analysis to identify significant effects and interactions, and leveraging parallel computing to manage computational demands [31] [32]. For stochastic ABMs, ensure sufficient replications at each parameter combination to distinguish signal from noise [32].
Troubleshooting Common Issues
Problem: Inconsistent results across similar parameter values in ABM simulations. Solution: This may indicate numerical ill-conditioning or high sensitivity regions in your parameter space. Increase the number of replications per parameter set to distinguish stochastic variation from true instability. Implement a finer-grained sweep around the problematic values to map the sensitivity landscape more precisely. Check for interactions between parameters that might be causing unpredictable behavior [32].
Problem: Parameter sweeps are computationally expensive and time-consuming. Solution: Employ strategic sampling techniques rather than exhaustive sweeps when possible. Use preliminary screening designs (e.g., fractional factorial) to identify influential parameters before comprehensive sweeps. Leverage cloud computing or high-performance computing resources to parallelize simulations. Consider surrogate modeling or emulation to approximate model behavior between sampled points [31].
Problem: Difficulty interpreting the results from multi-dimensional parameter sweeps. Solution: Utilize dimensionality reduction techniques and advanced visualization. Create interaction plots to understand how parameters combine to affect outputs. Apply sensitivity analysis methods like the Extended One-Factor-at-a-Time (OFAT) or variance-based techniques to rank parameter importance. Focus on key emergent properties rather than trying to comprehend all output dimensions simultaneously [31] [32].
Comparison of Parameter Sweep Methodologies for ABM Analysis
Table 1: Sensitivity Analysis Methods for ABM Verification and Ill-Conditioning Detection
| Method | Key Features | Advantages | Limitations | Best Use Cases |
|---|---|---|---|---|
| Extended OFAT (One-Factor-at-a-Time) | Varies one parameter across wide range while others fixed [31] | Reveals nonlinear responses and tipping points; Intuitive interpretation [31] | Misses parameter interactions; Inefficient for many parameters [31] | Initial exploration; Understanding individual parameter effects [31] |
| Variance Decomposition (Sobol' indices) | Quantifies contribution of each parameter to output variance [31] | Captures interaction effects; Provides quantitative importance ranking [31] | Computationally intensive; Requires many evaluations [31] | Comprehensive importance analysis; Understanding interaction effects [31] |
| Factorial Design | Simultaneously varies multiple parameters using structured combinations [32] | Efficiently explores parameter space; Captures interactions [32] | Can become complex with many parameters; Resolution limitations [32] | Systematic screening of multiple parameters; Identifying interactions [32] |
| Morris Method | Global sensitivity screening using elementary effects | Computationally efficient; Good for screening many parameters | Less precise than variance-based methods | Initial screening of models with many parameters |
Table 2: Parameter Sweep Types and Their Applications in Pharmaceutical ABMs
| Sweep Type | Description | Parameter Increment Calculation | Number of Simulations | Pharmaceutical ABM Applications |
|---|---|---|---|---|
| Linear | Evenly spaced values between start and end [30] | (End - Start)/Increment [30] | (End - Start)/Increment [30] | Dose-response relationships; Concentration gradients [33] |
| Logarithmic (Decade) | Multiplicative steps by powers of 10 [30] | Start × 10^N until reaching end [30] | Number of decades × Points/decade [30] | Pharmacokinetic parameters (IC50, EC50); Binding affinities [33] |
| Octave | Multiplicative steps by factors of 2 [30] | Start × 2^N until reaching end [30] | Number of doublings [30] | Growth rate studies; Cell division parameters [33] |
| List | User-specified values [30] | Custom values separated by spaces, commas or semicolons [30] | Number of values in list [30] | Testing specific experimental conditions; Clinical trial scenarios [33] |
Experimental Protocols
Protocol 1: Comprehensive Parameter Sweep for ABM Verification
Purpose: To systematically identify numerical ill-conditioning and sensitivity regions in Agent-Based Models for drug development applications.
Materials: ABM simulation platform, high-performance computing resources, parameter configuration files, data logging framework, visualization software.
Methodology:
- Parameter Selection and Prioritization: Identify both parametric (numerical) and non-parametric (behavioral rules, network structures) elements for sweeping. Categorize by theoretical importance and empirical uncertainty [32].
- Sweep Design: Implement a multi-stage approach:
- Initial broad screening sweeps (wide ranges, coarse increments)
- Focused sweeps around sensitive regions (narrower ranges, finer increments)
- Interaction sweeps for critical parameter combinations [31]
- Execution: Implement automated sweep execution with:
- Checkpointing to save intermediate results
- Randomized run order to avoid sequence artifacts
- Sufficient replications per parameter set (typically 50-100 for stochastic ABMs)
- Analysis:
Validation: Compare sweep results with analytical solutions where available. Verify consistency across different random seeds. Cross-validate with alternative sensitivity analysis methods [32].
Protocol 2: Detection and Diagnosis of Numerical Ill-Conditioning
Purpose: To specifically identify and characterize numerical ill-conditioning in pharmaceutical ABMs.
Materials: As in Protocol 1, with additional statistical analysis tools for detecting instability.
Methodology:
- Local Sensitivity Analysis: Calculate partial derivatives of key outputs with respect to parameters at multiple points in parameter space [31].
- Condition Number Estimation: Compute condition numbers for the model by analyzing how output uncertainty amplifies input uncertainty:
- Condition Number = (Relative change in output) / (Relative change in input)
- Values >> 1 indicate potential ill-conditioning
- Stability Mapping: Perform very fine-grained sweeps in suspected problematic regions to map stability landscapes.
- Interaction Analysis: Use factorial designs to identify parameter interactions that contribute to instability [32].
Interpretation: Regions with rapidly changing sensitivities, high condition numbers, or strong interactions indicate ill-conditioning that may require model reformulation or parameter constraints.
Visualizations
Workflow for Parameter Sweep Analysis in ABM Verification
Sensitivity Analysis Decision Framework
Research Reagent Solutions
Table 3: Essential Computational Tools for Parameter Sweep Analysis in Pharmaceutical ABMs
| Tool Category | Specific Solutions | Function in Parameter Sweep Analysis | Application Context |
|---|---|---|---|
| ABM Platforms | NetLogo, Repast, MASON, AnyLogic | Provide environment for implementing agent-based models and conducting simulation experiments | Core modeling environment for pharmaceutical ABMs (e.g., tumor growth, immune response) [31] |
| Sensitivity Analysis Libraries | SALib (Python), R sensitivity package, SIMLAB | Implement various sensitivity analysis methods including Sobol' indices, Morris method, and Fourier amplitude testing | Quantitative assessment of parameter influences and interactions in complex ABMs [31] [32] |
| High-Performance Computing | SLURM, Apache Spark, Cloud computing platforms | Enable parallel execution of multiple parameter combinations to reduce computation time | Managing computational demands of extensive parameter sweeps for complex pharmaceutical ABMs [32] |
| Parameter Sweep Tools | Multisim Parameter Sweep, COMSOL Parametric Sweep, LTspice .step command | Built-in functionality for systematically varying parameters in simulation environments | Circuit-level analysis relevant to medical device development; Physical process modeling [30] [34] [35] |
| Data Analysis & Visualization | R, Python (Pandas, Matplotlib, Seaborn), Tableau | Analyze and visualize large datasets generated from parameter sweeps; Create ICE plots, sensitivity indices | Interpretation of sweep results; Identification of patterns and ill-conditioned regions [31] [32] |
| Version Control Systems | Git, Subversion | Track changes to model parameters and code during sweep experiments | Reproducibility and collaboration in ABM verification research [32] |
Optimizing Time-Step Convergence to Minimize Discretization Error
Frequently Asked Questions
FAQ 1: My simulation is taking an extremely long time due to very small automatic time steps. The solver log shows
NLfail > 0. What does this mean and how can I resolve it? TheNLfailcounter increments each time the nonlinear algebraic solver fails to converge within a time step [36]. This forces the time step to be reduced, drastically increasing computation time. To resolve this, you can:- Increase the maximum number of iterations for the algebraic solver [36].
- Change the Jacobian update policy to be more frequent, such as updating it once per time step or even once per iteration [36].
- For highly nonlinear problems, enable the nonlinear controller in the time-stepping settings, which will adopt a more conservative and robust time-step selection [36].
FAQ 2: How can I determine if my chosen time step and spatial mesh are adequate for achieving a sufficiently accurate solution? You should perform a mesh and time-step convergence analysis [36]. This involves running your simulation with progressively finer meshes and smaller time steps until the key output variables of interest (e.g., maximum point error, integral error) show negligible changes. The table below, from a Burgers' equation example, shows how error changes with mesh size (
h_max) and solver relative tolerance (R), guiding the selection of adequate discretization parameters [36].FAQ 3: Why would making the solver tolerance stricter (smaller) sometimes lead to larger time steps and a faster simulation? This seemingly counter-intuitive behavior occurs because a larger solver tolerance can lead to a larger algebraic error, which perturbs the temporal error estimate [36]. This perturbation can cause the BDF solver to unnecessarily reduce its order or the time step to control the perceived error. A stricter tolerance reduces this algebraic noise, allowing the solver to confidently take higher-order, larger steps, ultimately making the time-stepping more efficient [36].
FAQ 4: What is the fundamental difference between explicit and implicit time discretization methods, and when should I choose one over the other? The core difference lies in how they handle future state information for calculating the current time step's solution [37].
- Explicit Methods use known information from previous time steps to compute the new state. They are computationally cheap per step but are only conditionally stable, requiring the time step
Δtto be smaller than a certain limit (often related to the Courant–Friedrichs–Lewy condition) [37] [38]. - Implicit Methods formulate the equations for the new time step in terms of both known and unknown future states, requiring the solution of a system of equations at each step. They are more computationally expensive per step but are often unconditionally stable, allowing for larger time steps [37]. You should choose an explicit method for fast, wave-dominant problems where a small time step is acceptable. Choose an implicit method for stiff problems (e.g., involving multiple timescales) where stability is a primary concern.
- Explicit Methods use known information from previous time steps to compute the new state. They are computationally cheap per step but are only conditionally stable, requiring the time step
Troubleshooting Guides
Guide 1: Addressing Poor Convergence and Small Time Steps
Symptoms: Simulation runs very slowly, the solver log shows many failed steps (NLfail > 0 or Tfail > 0), and the automatic time step becomes very small [36].
| Step | Action | Expected Outcome & Rationale |
|---|---|---|
| 1. Diagnose | Check the solver log for NLfail and Tfail counts. A high NLfail indicates the nonlinear algebraic solver is struggling to converge [36]. |
Identifies the root cause as either a nonlinearity issue (NLfail) or a time integration error issue (Tfail). |
2. Adjust Solver (if NLfail > 0) |
Increase the algebraic solver's maximum iteration count. Consider switching to a more robust nonlinear solver or adjusting its damping factor [36]. | Gives the algebraic solver more opportunity to converge within a time step, preventing unnecessary step reductions. |
| 3. Adjust Time Stepping | Enable the nonlinear controller in the time-stepping settings [36]. | Makes the time-step controller more conservative for highly nonlinear problems, proactively avoiding steps that are too large and would cause solver failure. |
| 4. Verify Parameters | Perform a convergence analysis on your model to ensure your mesh and initial time-step settings are reasonable for the physics. | Rules out fundamental undersampling in space or time as the cause of instability. |
Guide 2: Performing a Convergence Analysis for Discretization Error Control
Objective: Systematically quantify and minimize errors arising from spatial and temporal discretization.
| Step | Protocol | Key Metrics & Outputs | ||||
|---|---|---|---|---|---|---|
| 1. Generate Reference | Run your simulation with the finest mesh and smallest time step that is computationally feasible. This serves as your reference solution, u_ref [36]. |
A high-fidelity solution against which coarser solutions are compared. | ||||
| 2. Refine Systematically | Run a series of simulations with progressively coarser spatial meshes (h_max) and larger solver relative tolerances (R). Keep a detailed record of the computational cost for each run [36]. |
A set of solutions at different discretization levels. | ||||
| 3. Quantify Error | For each simulation, compute error metrics against the reference solution. Common metrics include:• Maximum Point Error: `e_P := max | u(t,x) - u_ref(t,x) | <br>• Integral Error:e_I := ∫ |
u(t,x) - u_ref(t,x) | dx` [36]. | Quantitative error data linking discretization parameters to solution accuracy. |
| 4. Analyze & Select | Plot the error metrics and computational cost against the discretization parameters. Identify the point where further refinement yields diminishing returns (error saturation) [36]. | A justified set of discretization parameters that provides the required accuracy with minimal computational cost. |
The table below illustrates a sample result from such an analysis, helping to identify the "sweet spot" for parameters (highlighted in green), where error is minimized without excessive computational cost.
Table: Sample Convergence Analysis for a Model Problem (adapted from [36])
Relative Tol. (R) |
Mesh Size (h_max) |
# Time Steps | Max Point Error (e_P1) |
Max Point Error (e_P2) |
Integral Error (e_I) |
|---|---|---|---|---|---|
| 0.01 | 1e-2 | 106 | 1.5e-2 | 4.9e-1 | 8.1e-3 |
| 0.001 | 1e-3 | 246 | 6.0e-3 | 1.6e-1 | 1.8e-3 |
| 0.0001 | 1e-4 | 461 | 1.7e-3 | 1.2e-3 | 8.3e-5 |
| 0.00001 | 1e-5 | 855 | 9.8e-9 | 6.3e-8 | 3.5e-9 |
The Scientist's Toolkit: Key Research Reagent Solutions
The following computational tools and concepts are essential for conducting robust numerical experiments in the context of Agent-Based Model (ABM) verification and discretization error analysis.
Table: Essential Computational Reagents for Discretization Error Analysis
| Item / Concept | Function in the "Experiment" |
|---|---|
| Backward Differentiation Formula (BDF) | An implicit, multi-step time-stepping method known for its stability, especially for stiff problems. Its order is automatically adjusted based on local error estimates [36]. |
| Method of Lines | A technique that discretizes a PDE in all but one dimension (typically space), converting it into a large system of ODEs or DAEs which can then be integrated with mature time-stepping methods [39]. |
| Finite Difference Approximations | Formulas used to approximate derivatives at discrete grid points. The choice between forward, backward, and central differences affects the accuracy and stability of the spatial discretization [39] [37]. |
Solver Relative Tolerance (R) |
A user-defined parameter that sets the target accuracy for the solver. It directly influences both the time-discretization error and the termination criterion for algebraic iterations [36]. |
| Convergence Analysis | The systematic procedure of refining spatial and temporal discretization to estimate and control the numerical error, ensuring the computed solution approximates the true continuous solution [36]. |
| Lax Equivalence Theorem | A fundamental theorem stating that for a consistent numerical scheme, stability is the necessary and sufficient condition for convergence [38]. |
Methodological Protocols
Protocol 1: Quantifying Discretization Error via Mesh Convergence This protocol is critical for verifying that your ABM's dynamics are not artifacts of the numerical discretization.
- Generate Reference Data: Compute a reference solution
u_refusing a spatial mesh sizeh_refand a time-step solver toleranceR_refthat are significantly finer/stricter than those used in production runs [36]. - Parameter Sweep: Execute a series of simulations where you vary the primary discretization parameters (e.g., maximum mesh size
h_max, solver relative toleranceR). Record the number of time steps taken and the computational time for each run [36]. - Error Calculation: For each output of interest, calculate global error metrics such as the maximum point error and the integral error over the domain and simulation time, comparing against
u_ref[36]. - Analysis: Plot the error as a function of the discretization parameters and computational cost. The goal is to identify the region where the error is acceptably small and has converged, indicating that the solution is insensitive to further refinement.
Protocol 2: Stabilizing Nonlinear Solver Interactions This protocol addresses the common issue where nonlinear solver failures force the time step to become impractically small.
- Intervention Points: The key is to intervene in the solver's configuration to prevent
NLfail[36]. - Algebraic Solver Tuning:
- Jacobian Update Strategy: Change the
Jacobian updatepolicy fromMinimaltoOnce per time steporOnce per iteration. While more computationally expensive per iteration, this ensures the solver uses current derivative information, which can drastically improve convergence for strongly nonlinear problems [36].
Visualizing the Optimization Workflow
The following diagram illustrates the logical workflow and feedback mechanisms involved in diagnosing and optimizing time-step convergence, integrating the FAQs and troubleshooting guides into a single, actionable pathway.
Diagram Title: Time-Step Convergence Optimization Pathway
Frequently Asked Questions (FAQs)
What is the fundamental "signal-to-noise" problem in stochastic ABMs? The difference between two simulation runs contains both real mechanistic effects from parameter changes and stochastic noise from random number misalignment. Even with identical seeds, if one simulation uses a random number for a decision that the other doesn't, all subsequent random draws become misaligned, making small but meaningful outcome differences difficult to detect [40].
Why do traditional common random number (CRN) approaches fail for general ABMs? Traditional CRN maintains correlation only until the first difference between simulations occurs. After that, the random number sequences rapidly desynchronize as simulations consume random numbers for different purposes. Most ABMs use a single centralized random number stream, making them vulnerable to this cascading misalignment [40].
How can I achieve true common random numbers for agent-based modeling? Recent methodology implements separate pseudo-random number streams for each decision type, combined with time-step-dependent stream jumping and slot-based assignment. This ensures each agent decision uses precisely aligned random numbers across simulation scenarios, eliminating misalignment noise [40].
What are the benefits of eliminating random number noise? With perfectly aligned counterfactuals, differences between scenarios reflect only mechanistic effects of parameter changes, not random variation. This enables meaningful individual-level analysis, reduces the number of simulations needed for statistical significance, and prevents misleading conclusions where beneficial interventions appear harmful due to noise [40].
Troubleshooting Guide
Problem: High Variance in Intervention Effect Estimates
Symptoms: Large confidence intervals around effect size estimates, inconsistent directional effects across simulation runs, difficulty detecting small but meaningful intervention effects.
Solution: Implement the multi-stream Common Random Numbers framework:
- Create Decision-Specific Random Streams: Replace your single random number generator with multiple independent streams, one for each stochastic decision (infection, duration, treatment allocation, etc.). Use a unique name string for each decision, hashed to create seed offsets from your master seed [40].
- Implement Time-Step Stream Jumping: At the start of each time step, reset each decision stream to its initial state, then use "jump" functions to advance each stream as if
kdraws had been used, wherekis the current time step. This ensures time-aligned random numbers [40]. - Apply Slot-Based Random Assignment: Assign each agent a permanent "slot" number (typically based on unique ID). When sampling random numbers for a decision, generate an array of random values and assign them to agents by slot index, ensuring consistent random number assignment across scenarios [40].
- Limit Random Number Calls: Call each decision-specific stream at most once per time step, even if sampling random numbers for multiple agents [40].
Table: Configuration of Decision-Specific Random Streams
| Decision Type | Stream Name | Distribution | Used For |
|---|---|---|---|
| Infection Event | infection_risk |
Bernoulli | Determining transmission |
| Disease Duration | duration |
Gamma/Log-normal | Incubation, recovery time |
| Intervention Allocation | treatment_assignment |
Bernoulli/Categorical | Drug, vaccine assignment |
| Phenotype Switching | phenotype_switch |
Poisson/Gillespie | Cell state changes [27] |
Problem: Irreproducible Results Across Research Teams
Symptoms: Inability to replicate published findings, divergent outcomes with supposedly identical parameters, difficulties in model validation.
Solution: Enhance reproducibility through rigorous random number management:
- Document Full Random Number Framework: Beyond the master seed, document all decision stream names, jumping algorithms, and assignment methodologies in supplemental materials [41].
- Implement Seed-Set Protocols: Establish standard procedures for setting and recording master seeds across all simulation scenarios to enable exact replication.
- Version Control Random Number Components: Treat random number generation code as critical infrastructure, with strict version control to prevent algorithmic drift.
- Validate with Known Ground Truth: Use simple test cases with predictable outcomes to verify that your CRN implementation eliminates stochastic noise in differences [41].
Problem: Computational Overhead from Variance Reduction
Symptoms: Unacceptable simulation slowdown, memory constraints from storing multiple random streams, impractical computation times for parameter sweeps.
Solution: Optimize the implementation:
- Selective CRN Application: Apply full CRN only to decisions most sensitive to outcome variance (e.g., initial infection events), while using traditional methods for less critical decisions.
- Efficient Random Number Generation: Utilize modern, high-performance random number generators like PCG64DXSM that support fast jumping [40].
- Batch Sampling: Leverage vectorized operations to sample random numbers for all agents in a single call to each decision stream each time step [40].
- Emulator Development: For extensive parameter exploration, use history matching and Gaussian process emulation to reduce the number of full ABM runs required [42].
Research Reagent Solutions
Table: Essential Computational Tools for Stochasticity Management
| Tool/Technique | Function | Implementation Example |
|---|---|---|
| Multiple PRNG Streams | Provides independent random sources for different decision types | NumPy Random Generator with PCG64DXSM [40] |
| Stream Jumping | Advances PRNG state deterministically without generating all intermediate numbers | jumped() method in modern PRNG libraries [40] |
| Slot-Based Assignment | Ensures consistent random number assignment to agents across scenarios | Use agent UID modulo array size for indexing random arrays [40] |
| Gillespie Algorithm | Exact stochastic simulation for chemical reactions or phenotype transitions [27] | Next-reaction method for stochastic phenotype switching [27] |
| History Matching | Efficient model calibration to observed data using emulation | Combines heteroskedastic Gaussian processes with approximate Bayesian computation [42] |
| Mean-Field Limits | Derives deterministic PDE approximations from stochastic rules | Moment-closure methods connecting microscale randomness to macrodynamics [27] |
Experimental Workflow for Stochasticity Control
The following diagram illustrates the complete workflow for implementing common random numbers in agent-based models:
Relationship to Existence and Uniqueness Analysis
The management of stochasticity directly supports the broader thesis of ABM verification by enabling rigorous analysis:
Effective stochasticity control enables the rigorous analysis required for existence and uniqueness proofs in several ways:
- Validated Mean-Field Limits: By providing noise-free comparisons between stochastic ABMs and derived partial differential equation systems, researchers can rigorously verify when continuum approximations accurately capture microscale dynamics [27].
- Parameter Space Exploration: Efficient sensitivity analysis through controlled stochasticity enables comprehensive mapping of model behavior to input parameters, supporting existence arguments across parameter ranges [42].
- Numerical Analysis Foundation: Controlled random number alignment provides the consistent numerical experimentation platform needed to analyze discretization schemes, stability, and convergence properties of hybrid PDE-ABM systems [27].
Strategies for Handling Model Stiffness and Discontinuities
Frequently Asked Questions (FAQs)
FAQ 1: What are the primary sources of model stiffness and discontinuities in Agent-Based Models (ABMs)?
Model stiffness in ABMs often arises from multiscale dynamics, where processes occur at vastly different time scales. For instance, in a hybrid PDE-ABM modeling angiogenesis, fast stochastic phenotype switching (using a Gillespie algorithm) couples with slower reaction-diffusion fields for oxygen and nutrients, creating numerical challenges. Discontinuities are frequently introduced by discrete, rule-based agent decisions, such as a cell abruptly changing migration direction upon reaching a bifurcation point in a microfluidic environment [43] [27].
FAQ 2: How can global sensitivity analysis help manage parameter-induced stiffness?
Global sensitivity analysis identifies which input parameters most significantly impact model outputs. Parameters with high sensitivity indices are often linked to processes that cause stiffness. Using a method like SMoRe GloS (Surrogate Modeling for Recapitulating Global Sensitivity) allows for efficient exploration of the parameter space. By replacing the computationally expensive ABM with an explicitly formulated surrogate model, you can rapidly pinpoint critical parameters. Fixing or constraining these high-sensitivity parameters during specific simulation phases can mitigate stiffness [44].
FAQ 3: What role do hybrid modeling frameworks play in resolving these issues?
Hybrid frameworks (e.g., coupling ABMs with Partial Differential Equations (PDEs)) provide a rigorous mathematical structure to handle multiscale dynamics. The continuum (PDE) component can efficiently handle smooth, large-scale fields (e.g., nutrient concentrations), while the discrete (ABM) component captures individual agent stochasticity. This separation allows for the application of specialized numerical solvers suited to each component, thereby managing stiffness. Furthermore, deriving the mean-field limit of the ABM—a deterministic PDE description of the average agent behavior—provides an analytically tractable benchmark to verify the stochastic model and identify regions of potential instability [27].
FAQ 4: Can machine learning integration assist with discontinuous decision-making?
Yes, reinforcement learning (RL) can model complex cellular decision-making without hard-coded, discontinuous rules. In a model of barotactic cell migration, a Deep Q-Network (DDQN) learns to direct cell movement based on sensed pressure gradients. The neural network outputs probabilities for discrete actions, effectively "smoothing" the decision process. This learned, data-driven policy can be more numerically stable than a predefined conditional rule that triggers abrupt state changes [43].
Troubleshooting Guides
Issue 1: Unstable or Non-Convergent Simulation Results
Problem: Your ABM simulation crashes or produces erratic, non-physical results, often due to stiffness from multiscale interactions or discontinuous agent rules.
Solution:
- Step 1: Perform Global Sensitivity Analysis. Use the SMoRe GloS method to identify parameters whose uncertainty most significantly affects the unstable output. This prioritizes parameters for calibration.
- Protocol: Sample ABM parameter space using Latin Hypercube Sampling (LHS). Run multiple simulations at each sampled parameter vector to get averaged behavior. Fit an explicit surrogate model (e.g., a polynomial) to the ABM output. Use a variance-based method (e.g., eFAST) on the surrogate to compute global sensitivity indices [44].
- Step 2: Derive a Mean-Field Limit. For the agent-based dynamics, use moment-closure methods to derive a continuum PDE approximation. This mean-field limit serves as a verifiable ground truth for the average system behavior.
- Protocol: Formulate a master equation describing the probability of agent state transitions. Apply a moment-closure approximation to obtain a closed set of PDEs for the first and second moments (e.g., mean density) of the agent population. Compare the ABM's aggregate output to the solutions of these PDEs to identify discrepancies and isolate the source of instability [27].
- Step 3: Implement Hybrid Numerical Schemes. For hybrid PDE-ABM systems, use specialized time-stepping that treats the stiff (fast) components implicitly and the non-stiff (slow) components explicitly.
Issue 2: Handling Discontinuous and Stochastic Agent Transitions
Problem: Sharp, discrete changes in agent state (e.g., phenotype switching, directional change) cause numerical artifacts and make it difficult to analyze or calibrate the model.
Solution:
- Step 1: Replace Hard-Coded Rules with a Learned Policy. Integrate a Deep Reinforcement Learning (DRL) framework. Instead of a rule like "IF pressure > threshold, THEN turn," an agent uses a neural network to map its state (e.g., sensed pressures) to a probability distribution over possible actions.
- Protocol:
- Define State and Action Spaces: The state is a vector of environmental cues (e.g., pressure at multiple points around a cell). The action space is a set of discrete migration directions [43].
- Train with DDQN: Use the Double Deep Q-Network algorithm to train the policy. The reward function should guide the agent toward the desired behavior (e.g., moving toward a pressure gradient) [43].
- Protocol:
- Step 2: Use an Exact Stochastic Simulation Algorithm. For intrinsic stochasticity like phenotype switching, use an exact algorithm like the Gillespie algorithm. This ensures the timing of discrete events is simulated correctly without the time-step dependencies that can introduce errors in simpler methods [27].
Quantitative Data and Methodologies
Table 1: Global Sensitivity Analysis of a Vascular Tumor Growth ABM using SMoRe GloS
This table summarizes the application of the SMoRe GloS method to a complex 3D ABM, identifying parameters that could contribute to model stiffness [44].
| ABM Parameter | Description | Probability Distribution | Global Sensitivity Index (eFAST) | Computational Time (Direct eFAST) | Computational Time (SMoRe GloS) |
|---|---|---|---|---|---|
ProlifRate |
Cell proliferation rate | Uniform(0.5, 1.5) | 0.72 | ~ 72 hours | ~ 15 minutes |
DrugDiffusion |
Drug diffusion coefficient | LogNormal(1.0, 0.2) | 0.65 | ~ 72 hours | ~ 15 minutes |
ApoptosisThreshold |
Threshold for cell death | Normal(0.3, 0.05) | 0.21 | ~ 72 hours | ~ 15 minutes |
CellMotility |
Base cell movement speed | Uniform(0.1, 2.0) | 0.18 | ~ 72 hours | ~ 15 minutes |
Table 2: Key Research Reagent Solutions for Cell Migration and ECM ABMs
This table details essential computational "reagents" for building and analyzing models in this field [43] [27] [45].
| Research Reagent | Function in Modeling | Example Usage |
|---|---|---|
| Double Deep Q-Network (DDQN) | Learns optimal agent policies from environmental feedback, replacing hard-coded rules that cause discontinuities. | Predicting barotactic cell migration in response to pressure gradients [43]. |
| Gillespie Algorithm | Accurately simulates the timing of stochastic state transitions (e.g., phenotype switching) in a numerically exact manner. | Modeling stochastic resistance evolution in tumor cell populations [27]. |
| Explicit Surrogate Model (SMoRe GloS) | A computationally efficient, explicitly formulated model (e.g., polynomial) that approximates ABM output for rapid parameter screening. | Performing global sensitivity analysis on a 3D vascular tumor growth ABM [44]. |
| ECM Microstructure Framework | Represents the Extracellular Matrix via density, anisotropy, and orientation variables to model cell-ECM interactions. | Simulating cellular invasion, wound healing, and basement membrane degradation [45]. |
Experimental Protocols
Protocol 1: Training an ABM with Deep Reinforcement Learning
Objective: To train an agent in a barotactic cell migration ABM to respond to pressure gradients without predefined rules [43].
- Environment Setup: Define the microfluidic device geometry. Perform a Computational Fluid Dynamics (CFD) simulation to obtain the static pressure field, P(x).
- Agent Design: Represent the cell as an agent. Place equidistant observation points on its membrane to sense local fluid pressure.
- RL Integration:
- State (s): A vector of pressure values sensed at the observation points.
- Action (a): A set of discrete migration directions (e.g., towards 8 evenly distributed points around the cell).
- Reward (r): A function based on the agent's movement toward the goal location (e.g., the channel outlet).
- Training: Simulate the agent in multiple training geometries. Use the DDQN algorithm to update the weights of the neural network that maps states to action probabilities. Training is complete when the mean reward per episode approaches 1.0 [43].
Protocol 2: Deriving a Mean-Field Limit for an ABM
Objective: To derive a continuum PDE model from a stochastic ABM for verification and analysis purposes [27].
- Formulate the Master Equation: Write down the equation governing the probability of the entire ABM system being in a specific state at a given time. This describes all possible agent interactions and state transitions.
- Define Moment Equations: Derive equations for the time evolution of the first moment (mean density) and second moments (spatial correlations) of the agent population from the master equation.
- Apply Moment Closure: The equations for lower-order moments will depend on higher-order moments. Use a moment-closure approximation (e.g., a mean-field assumption that neglects correlations) to obtain a closed system of PDEs.
- Analysis and Verification: Analyze the well-posedness (existence and uniqueness of solutions) of the resulting PDE system. Numerically solve the PDEs and compare the solution to the average output of many ABM realizations to verify the ABM's correctness.
Workflow and System Diagrams
Diagram 1: Hybrid PDE-ABM Workflow for Angiogenesis
Diagram Title: Angiogenesis Feedback Loop
Diagram 2: SMoRe GloS Sensitivity Analysis
Diagram Title: Efficient Global Sensitivity Analysis
Benchmarking and Validating Your ABM's Numerical Solution
Frequently Asked Questions (FAQs)
Q1: What does "existence and uniqueness" mean in the context of ABM verification, and why is it a foundational step? Existence and uniqueness analysis is a core component of the deterministic verification workflow for Agent-Based Models [7]. It ensures that for any given set of reasonable input parameters, the computational model consistently produces a solution (existence) and that this solution is reproducible, with only minimal variations due to numerical rounding errors (uniqueness) [7]. This step provides the initial confidence that the model's core mechanics are robust before examining its emergent behaviors.
Q2: My model produces different global outcomes with identical parameters and random seeds. What should I check? This indicates a potential failure in uniqueness. Your verification protocol should include running the model multiple times with identical inputs and seeds, then comparing outputs [7]. Quantify the variation using appropriate statistical tests. If variation exceeds tolerances (e.g., beyond expected numerical rounding errors), investigate sources of non-determinism, such as uncontrolled external API calls, unseeded random number generators, or parallel processing race conditions.
Q3: How can I formally link emergent system-level behaviors back to specific agent rules during validation? A formalism exists for this purpose, which defines event types that characterize sets of behavioral 'motifs' at any level of abstraction [46]. This allows you to formulate and test specific hypotheses about associations between multi-level behaviors. For instance, you can design experiments to see if a specific agent interaction rule (e.g., "keep agent A between self and agent B") is a necessary and sufficient condition for an emergent group behavior (e.g., "cluster formation") to appear [47] [46].
Q4: What is a practical method for testing if my ABM is overly sensitive to small changes in input parameters? Perform a parameter sweep analysis [7]. This involves systematically sampling the input parameter space to identify regions where the model either fails to produce a valid solution or produces valid but unexpectedly large changes in output for small changes in input. For a more rigorous, stochastic assessment, use global sensitivity analysis techniques like LHS-PRCC (Latin Hypercube Sampling - Partial Rank Correlation Coefficient) to quantify each parameter's influence on key outputs [7].
Troubleshooting Guides
Issue 1: Failure of Uniqueness Analysis
Symptoms: The model yields significantly different results across multiple runs with identical parameters and random seeds.
Diagnostic and Resolution Protocol:
- Isolate Stochastic Elements: Temporarily replace all stochastic functions (e.g.,
rand()) with fixed, deterministic values. If the output stabilizes, the issue lies in the management of randomness. - Audit the Random Number Generator (RNG):
- Ensure the RNG is properly seeded at the start of each simulation.
- Verify that the same RNG sequence is used for identical runs.
- Confirm that no part of the code resets or re-seeds the RNG unintentionally.
- Check for External Influences: Identify and eliminate dependencies on system clocks, uncontrolled file I/O, or other external state not captured by the random seed.
- Review Parallel Processing: If the model uses parallel or concurrent execution, check for race conditions where the order of agent updates might vary between runs despite an identical seed. Consider using a fixed execution order for verification purposes.
Issue 2: Emergent Behavior is Absent or Counterintuitive
Symptoms: The system-level outcome does not match theoretical expectations or empirical data, or no clear pattern emerges from agent interactions.
Diagnostic and Resolution Protocol:
- Validate Agent-Level Rules Individually: Use unit testing to verify that each agent's internal logic and decision-making rules function as designed in isolation. The VOMAS (Virtual Overlay Multi-agent System) approach can be useful here, where "validator agents" monitor and log the actions of simulation agents against predefined constraints in real-time [48].
- Decouple Interaction Complexity:
- Begin validation with a minimal number of agent types (ideally one).
- Gradually reintroduce agent diversity and interaction rules, validating emergent patterns at each step. This bottom-up approach helps identify the specific rule or interaction that causes the deviation.
- Check for Scale-Dependent Effects: Run the simulation at different population sizes. The absence of expected emergence at small scales might be normal, but its persistent absence at larger scales indicates a fundamental flaw in the interaction rules.
- Calibrate with Sensitivity Analysis: Use LHS-PRCC or Sobol sensitivity analysis to identify which agent-level parameters have the strongest influence on the system-level output. This pinpoints the rules that require the most careful calibration [49] [7].
Issue 3: Model is Ill-Conditioned or Numerically Unstable
Symptoms: The model crashes, produces nonsensical values (e.g., negative populations), or shows extreme sensitivity to tiny parameter changes or the simulation time step.
Diagnostic and Resolution Protocol:
- Perform a Time Step Convergence Analysis: Run the model with progressively smaller time steps (
dt). Calculate the discretization error for key output quantities. The model is considered converged when this error falls below an acceptable threshold (e.g., 5%) [7]. Failure to converge suggests the numerical integration method is unstable. - Conduct a Smoothness Analysis: Calculate the coefficient of variation
Dfor output time series. A highDvalue indicates potential stiffness, singularities, or discontinuities in the solution, often resulting from faulty conditional logic or miscalculated rates in agent state transitions [7]. - Implement Boundary Guards: Code sanity checks within agent rules to prevent biologically or logically impossible states (e.g., a cell dividing when its energy is zero). These guards should log violations for debugging.
- Parameter Bound Checking: Systematically perform parameter sweeps to map the "valid operation" region of your parameter space and identify combinations that lead to failure [7].
Experimental Protocols for Key Analyses
Protocol 1: Deterministic Verification via Existence and Uniqueness
Objective: To prove that the ABM produces a valid and reproducible output for a given input space.
Methodology:
- Define Parameter Ranges: Establish the physiologically or logically plausible range for each input parameter.
- Existence Test: Execute the model across a large sample of the input space (e.g., using Latin Hypercube Sampling). A successful test is one where the model completes without crashing and produces an output within expected bounds for all samples.
- Uniqueness Test:
- Select a representative subset of input parameter sets from the existence test.
- For each set, run the model N times (e.g., N=10) using the same random seed.
- For a key output metric
Q(e.g., final tumor size), calculate the coefficient of variation (CV = Standard Deviation / Mean) across the N runs. - Success Criterion: The CV for
Qshould be negligible, typically below a pre-defined threshold (e.g., 0.1%), indicating that numerical noise does not significantly affect the result [7].
Protocol 2: Linking Agent Rules to Emergent Behavior
Objective: To formally validate that a specific agent-level rule is responsible for an observed system-level phenomenon.
Methodology:
- Hypothesis Formulation: State a clear, testable hypothesis. Example: "The emergent behavior 'cluster formation' is causally linked to the agent-level rule 'move to keep agent A between self and agent B'."
- Define Behavioral Events: Formalize both the agent-level rule and the system-level behavior as detectable events or "behavioral motifs" that can be logged during simulation [46].
- Controlled Experiment:
- Control Group: Run the simulation with the rule enabled.
- Intervention Group: Run the simulation with the rule disabled or mutated.
- Association Analysis: Use statistical methods (e.g., correlation analysis, Granger causality) to test the strength of association between the frequency or timing of the agent-level events and the emergence of the system-level behavior across multiple runs [46].
- Validation: A strong, statistically significant association in the control group that disappears in the intervention group provides evidence for the causal link.
Quantitative Verification Criteria Table
The following table summarizes key metrics and their success criteria for a robust multi-level validation.
| Analysis Type | Key Metric | Calculation | Success Criterion | Reference |
|---|---|---|---|---|
| Time Step Convergence | Discretization Error | e_q = (q_i* - q_i) / q_i* * 100Where q_i* is output at reference time-step, q_i at larger time-step. |
e_q < 5% |
[7] |
| Smoothness Analysis | Coefficient of Variation (D) | Standard deviation of the first difference of the time series, scaled by the absolute mean. | A low D value, indicating no sharp, unbuffered transitions. |
[7] |
| Uniqueness Analysis | Coefficient of Variation (CV) | CV = (Standard Deviation of N identical runs) / Mean |
CV < 0.1% (or other pre-defined negligible threshold) | [7] |
| Parameter Sweep | Model Robustness | Percentage of input parameter space that produces valid, expected outputs. | High percentage (>95%) of valid outputs within the plausible parameter space. | [7] |
The Scientist's Toolkit: Research Reagent Solutions
| Tool or Technique | Function in ABM Verification | Application Context |
|---|---|---|
| Virtual Overlay Multi-Agent System (VOMAS) | A framework for real-time validation where "validator agents" monitor simulation agents for constraint violations. | Useful for verifying agent-level rules and logging interactions during runtime for later analysis [48]. |
| Latin Hypercube Sampling (LHS) | An efficient, stratified sampling technique to explore the multi-dimensional parameter space with fewer runs. | Used for parameter sweep analysis and to generate input for sensitivity analysis (e.g., LHS-PRCC) [7]. |
| Partial Rank Correlation Coefficient (PRCC) | A global sensitivity measure that quantifies the monotonic, non-linear influence of an input parameter on an output. | Identifying which agent-level parameters have the strongest effect on system-level emergent behavior [7]. |
| Model Verification Tools (MVT) | An open-source software suite that automates key deterministic verification steps like convergence and smoothness analysis. | Provides a standardized computational workflow for ABM verification, ensuring robustness and correctness [7]. |
| Gillespie Algorithm | An exact stochastic simulation algorithm that rigorously models random phenotype transitions and their timing. | Essential for accurately modeling stochastic intracellular processes (e.g., resistance mutations) in hybrid biological ABMs [27]. |
| Moment-Closure Methods | Mathematical techniques to derive a tractable mean-field PDE description from the stochastic rules of an ABM. | Connecting microscale agent randomness to macroscale, deterministic population dynamics for analytical insight [27]. |
Workflow Visualization
Deterministic ABM Verification Workflow
Multi-Level Validation Logic
Technical Support Center: ABM Verification & Validation
Frequently Asked Questions
Q: What is the primary purpose of benchmarking an Agent-Based Model (ABM) against a known analytical solution?
A: Benchmarking serves to verify that the mechanistic rules and algorithms governing individual agent behaviors correctly produce the expected system-level dynamics. This process builds credibility in your model's predictive capabilities, which is especially critical when model outputs inform high-stakes decisions, such as in drug development or regulatory submissions [8]. A successful benchmark demonstrates that your ABM, despite its potential complexity, can reproduce established truths, providing a foundation for exploring novel scenarios where analytical solutions are unavailable.
Q: In a pharmacological context, when is an ABM particularly advantageous over other modeling techniques?
A: ABM is uniquely advantageous when the system of interest is characterized by significant heterogeneity, spatial structure, and emergent behaviors that are not easily captured by averaged population-level models. They provide a platform for integrating knowledge across spatiotemporal scales—from molecular interactions to tissue-level response—and can incorporate stochasticity to understand how patient variability arises from fundamental mechanisms [10] [50]. This makes them ideal for probing complex biological processes like tumor formation, immune response, and organ-level toxicity.
Q: Our ABM reproduces a known analytical solution. What is the next step in the validation process?
A: Reproducing an analytical solution is a key verification step. Subsequent validation should focus on testing the model's ability to reproduce multiple, independent empirical patterns not used in the model's construction [51]. This could include longitudinal data from clinical trials or novel, out-of-sample phenotypes observed in preclinical studies. The goal is to evaluate the model's predictive power in a broader context, strengthening its credibility for a specific Context of Use [8].
Q: What are the best practices for documenting the verification and validation of an ABM for a regulatory audience?
A: Adherence to established technical standards is paramount. You should clearly define the Context of Use—the specific regulatory question the model is intended to inform. Following this, a comprehensive process of Verification, Validation, and Uncertainty Quantification (VVUQ) must be documented. This involves rigorous code verification, validation against relevant experimental data, and a thorough analysis of how uncertainty in model inputs and parameters propagates to uncertainty in the predictions. Frameworks like the ASME V&V-40 provide detailed guidance on this process for regulatory submission [8].
Troubleshooting Guides
Issue 1: Model Fails to Replicate Known System Dynamics
Problem: During benchmarking, your ABM does not converge to or produce the system-level behavior described by a known analytical solution or a well-established ODE model.
Diagnosis and Resolution:
- Step 1: Verify Agent Rules. Scrutinize the rules governing individual agent behaviors and state transitions. Ensure they are implemented correctly in the code. A common error is a mismatch between the conceptual biological hypothesis and its algorithmic implementation [10] [51].
- Step 2: Check Spatial and Temporal Parameters. If benchmarking against an ODE, confirm that your spatial parameters (e.g., agent density, grid size) and temporal parameters (e.g., time steps) are configured to approximate a "well-mixed" system. Discrepancies can often be traced to spatial effects not present in the analytical solution.
- Step 3: Calibrate Stochasticity. For stochastic ABMs, run a sufficient number of simulations to ensure you are observing the expected mean population behavior. A single simulation run may not be representative. Use the results from multiple runs to generate confidence intervals around the mean output.
Issue 2: High Outcome Variability in a Deterministic System
Problem: The ABM shows high and unexpected variability in outcomes between runs, even when the system is expected to be largely deterministic based on the benchmark.
Diagnosis and Resolution:
- Step 1: Identify and Isolate Random Number Generators (RNGs). Pinpoint all parts of the code that rely on random number generation. Check that RNG seeds are being managed correctly to ensure true randomness is only applied where intended (e.g., in agent decision-making) and not in core mechanistic processes.
- Step 2: Review Initial Conditions. Ensure that all simulations start from identical initial conditions. Small, unintended variations in the initial state of agents or the environment can lead to divergent outcomes in complex systems.
- Step 3: Check for Edge Cases. Review agent interaction rules for edge cases or rare events that, while low in probability, could dramatically alter system dynamics when they occur. Implement logging to capture such events during simulation runs.
Issue 3: Inability to Reproduce Published Multi-Scale Phenomena
Problem: The ABM integrates mechanisms from different biological scales (e.g., molecular signaling and cellular proliferation) but fails to reproduce the published emergent tissue-level or organ-level phenotype.
Diagnosis and Resolution:
- Step 1: Validate Sub-Modules Independently. Decouple the multi-scale model and benchmark each sub-module (e.g., a signaling network) independently against its respective established data or model. This isolates the source of the failure [50].
- Step 2: Audit Knowledge Integration. The ABM serves as a platform for knowledge integration [10]. Systematically audit the literature-derived rules and parameters embedded in the model. It is possible that critical mechanistic data is missing, outdated, or incorrectly translated from the conceptual model to the computational framework.
- Step 3: Implement Pattern-Oriented Modeling (POM). Avoid calibrating to a single outcome. Instead, use a POM approach, where the model is simultaneously calibrated to and must reproduce multiple patterns observed at different scales of the system (e.g., cell count dynamics and spatial organization). This rigorously tests the model's structural realism and reduces equifinality [51].
Experimental Protocols & Methodologies
Case Study: Verification of an Intestinal Crypt ABM for Safety Pharmacology
This protocol outlines the verification of an ABM designed to predict chemotherapy-induced diarrhea (CID) by simulating injury and recovery in the human gastrointestinal crypt [50].
1. Purpose To verify that the in silico crypt ABM recapitulates core homeostatic and injury-response behaviors observed in vivo, establishing its credibility for predicting drug-induced gastrointestinal toxicity.
2. Computational Modeling Approach The ABM simulates individual cells (agents) within the crypt geometry. Each agent has internal rules governing its behavior (proliferation, differentiation, migration, death) based on local interactions with neighboring cells and signaling molecules (e.g., Wnt, Notch) [50].
3. Benchmarking Methodology
Step 1: Homeostasis Verification.
- Objective: Verify that the model maintains a stable population of stem, transit-amplifying, and differentiated cells over time without external injury.
- Procedure: Run the simulation for a prolonged virtual time (e.g., 30 days) with no interventions.
- Success Criteria: Cell populations and spatial organization along the crypt axis remain statistically stable, mimicking physiological turnover.
Step 2: Injury-Response Benchmarking.
- Objective: Benchmark the model's response against known analytical solutions and experimental data for radiation-induced injury.
- Procedure:
- Simulate exposure to a pulsed insult (e.g., a standardized radiation dose).
- Measure key output metrics: percentage of cell loss, time to repopulate the crypt, and dynamics of key recovery biomarkers.
- Success Criteria: The model's output falls within the confidence intervals of historical in vivo data or matches the trajectory of a validated, simpler mathematical model of crypt recovery.
Step 3: Hybrid Model Cross-Validation.
- Objective: Cross-validate the ABM against a hybrid model incorporating ODEs for specific signaling pathways [50].
- Procedure: For a specific pathway (e.g., Wnt signaling), replace the ABM's rule-based logic with an ODE sub-module that calculates the average signaling intensity. Compare the system-level output of this hybrid model to the pure ABM.
- Success Criteria: Both model versions produce qualitatively and quantitatively similar system-level behaviors, confirming the mechanistic consistency of the ABM's rules.
4. Key Quantitative Benchmarks The following table summarizes the success criteria for the core verification experiments.
| Model Behavior | Benchmark Metric | Target Value / Qualitative Outcome |
|---|---|---|
| Crypt Homeostasis | Stem cell count fluctuation | < 5% coefficient of variation over 30 days |
| Crypt Homeostasis | Cell migration velocity | Consistent with observed 5-7 day turnover in humans |
| Response to Injury | Time to 90% crypt repopulation | Matches established in vivo data (e.g., 7-10 days post-insult) |
| Pathway Inhibition | Effect of Wnt pathway suppression | Ablation of stem cell population and crypt collapse |
The Scientist's Toolkit: Essential Research Reagents & Materials
The following table details key computational and biological "reagents" essential for developing and verifying a pharmacological ABM, using the intestinal crypt as an example.
| Item Name | Type | Function in the Experiment |
|---|---|---|
| In Silico Crypt Template | Computational Geometry | A pre-defined spatial lattice that represents the physical structure of the intestinal crypt, providing the environment in which agents (cells) interact [50]. |
| Cell Agent Class Library | Core Model Code | Defines the base properties and behavioral rules (state machines) for stem, transit-amplifying, and differentiated cells [50]. |
| Signaling Pathway Module (Wnt/Notch) | Computational Sub-model | A plug-in component, often implemented with ODEs or stochastic rules, that simulates the concentration dynamics and influence of key morphogens on cell fate [10] [50]. |
| Virtual Assay: Cell Census | Analysis Script | A script that counts cells by type and location at each time step, generating the primary quantitative output for benchmarking against homeostatic data. |
| Virtual Assay: Damage Indicator | Analysis Script | A script that simulates the application of a chemotherapeutic or radiation insult to the crypt and tracks the subsequent metrics of injury and recovery. |
| Parameter Set: Human Crypt Homeostasis | Model Parameters | A curated set of parameters (e.g., cell cycle times, death rates) derived from literature that calibrates the model to normal human physiology [50]. |
Model Verification Workflow Diagram
Knowledge Integration in Multi-Scale ABM
Frequently Asked Questions
Q1: What is the primary purpose of sensitivity analysis in Agent-Based Model (ABM) verification? Sensitivity analysis serves several critical functions in ABM verification, extending beyond simple robustness checks. Its primary purposes are to:
- Understand Model Mechanisms: Uncover how patterns and emergent properties are generated from the model's rules and parameters [31].
- Assess Robustness: Examine whether the model's core findings and emergent properties hold under a range of different assumptions and parameter values [31].
- Quantify Uncertainty: Determine how much the uncertainty in the model's input parameters contributes to the variability of its outputs, allowing you to identify which parameters require more precise estimation [31].
- Identify Key Drivers and Interactions: Discover which model elements (both parametric and non-parametric) have the greatest impact on outcomes and how they interact with each other [32].
Q2: Why is sensitivity analysis particularly challenging for ABMs compared to other modeling approaches? ABMs possess inherent characteristics that complicate the application of standard sensitivity analysis methods [31] [32]. These challenges include:
- Multiple Levels: ABMs operate at both the micro-level (individual agents) and macro-level (system-wide outcomes), with no direct, pre-defined link between the two.
- Nonlinear Interactions: Agents interact in ways that often lead to nonlinear relationships between inputs and outputs.
- Emergent Properties: The most important outcomes often arise unpredictably from the interactions of simple agent rules, making it difficult to trace output changes back to specific inputs.
- Stochasticity: ABMs are inherently stochastic, meaning multiple runs with identical inputs can produce different outputs, requiring statistical analysis of results.
- Non-Parametric Elements: A model's core logic and agent behavioral rules are often non-parametric, making it difficult to vary them systematically for sensitivity testing [32].
Q3: My ABM is computationally expensive. How can I perform a thorough sensitivity analysis? For computationally intensive ABMs, a common strategy is to use surrogate modeling (also known as meta-modeling) [52]. This process involves:
- Running the original ABM a limited number of times across the parameter space.
- Using the results to train a simpler, computationally cheaper model (the surrogate) that approximates the ABM's input-output relationship.
- Performing extensive sensitivity analysis on the fast surrogate model.
A critical caution is that this procedure must be applied carefully. Surrogates can be misleading if the ABM's behavior is highly nonlinear or non-ergodic. A proposed protocol, Monte Carlo-Once-At-a-Time, can be used to intelligently select parameter ranges where the surrogate is a reliable proxy before proceeding with global sensitivity analysis [52].
Q4: How do I choose a sensitivity analysis method for my ABM? The choice of method depends on your primary goal. The table below summarizes recommended methodologies for common objectives.
| Analysis Goal | Recommended Methodologies | Key Strengths |
|---|---|---|
| Understand Mechanisms & Identify Tipping Points | Extended One-Factor-at-a-Time (OFAT) [31] | Simple to implement; reveals nonlinear response curves and tipping points by showing the relationship between a single parameter and output. |
| Rank Parameters by Influence & Detect Interactions | Variance-Based Methods (e.g., Sobol' indices) [31] [32] | Quantifies each parameter's contribution to output variance, including interaction effects between parameters. |
| Test Robustness of Conclusions | Factorial Design with Randomized Finite Change Indices [32] | Systematically varies multiple parameters (including non-parametric elements) simultaneously to test the stability of results. |
| Determine Direction of Change | Stochastic Individual Conditional Expectation (S-ICE) Plots [32] | A modification of ICE plots that accounts for the stochastic nature of ABMs, showing how outputs change directionally with a parameter. |
Q5: How does sensitivity analysis relate to other ABM verification steps, like checking for uniqueness? Sensitivity analysis is a core component of a comprehensive verification and validation framework. Its relationship to uniqueness analysis is especially close:
- A sensitivity analysis can reveal if different parameter combinations lead to similar system behaviors, which is informative for understanding the potential for non-unique model outcomes that still plausibly represent real-world phenomena [31].
- Conversely, it can also show if the model produces sharply different outcomes from only slight parameter changes, indicating potential tipping points and a lack of smoothness in the parameter-output relationship [31].
- In the context of a broader thesis on existence and uniqueness, sensitivity analysis provides the empirical evidence to support claims about how robust and general a model's findings are, which is critical for establishing its credibility [32].
Experimental Protocols
Protocol 1: Performing an Extended OFAT (One-Factor-at-a-Time) Analysis
Objective: To understand the fundamental relationship between individual model parameters and outputs, and to uncover potential nonlinearities and tipping points.
Materials: A functioning ABM simulation; a defined parameter space; a high-performance computing cluster or cloud resources for multiple simulation runs.
Workflow:
- Establish a Baseline: Select a nominal set of parameter values that represents your standard or best-estimate model configuration.
- Select Parameters and Ranges: Choose the parameters to analyze and define a biologically or socially plausible range for each.
- Iterate and Run: For each parameter selected, systematically vary its value across the defined range while keeping all other parameters fixed at their nominal values. Run the simulation multiple times at each value to account for stochasticity.
- Analyze and Plot: For each parameter, plot its values against the resulting model outputs (e.g., the mean of the final outcome). Analyze these plots for linear trends, thresholds, and tipping points.
Protocol 2: Implementing a Global Variance-Based Sensitivity Analysis
Objective: To quantify the contribution of each input parameter to the output variance, including interaction effects between parameters.
Materials: A functioning ABM; a defined parameter space; software for generating samples (e.g., Saltelli sample) and computing Sobol' indices.
Workflow:
- Generate Sample Matrix: Use a quasi-Monte Carlo method (e.g., the Saltelli sampling scheme) to generate a large number of parameter combinations from the defined multidimensional parameter space. This creates two base sample matrices.
- Execute Simulations: Run your ABM for each parameter combination in the sample matrices. The number of required runs is
N * (2 * D + 2), whereNis a base sample size (e.g., 1,024) andDis the number of parameters. - Compute Sensitivity Indices: Use the resulting output data to calculate the Sobol' indices.
- First-Order Indices (
S_i): Measure the fractional contribution of a single parameterito the output variance. - Total-Order Indices (
S_Ti): Measure the total contribution of parameteri, including all its interaction effects with other parameters.
- First-Order Indices (
- Interpret Results: Rank parameters by their indices. A large difference between
S_iandS_Tifor a parameter indicates significant interaction effects.
Research Reagent Solutions
The following table details key computational tools and concepts used in advanced ABM sensitivity analysis.
| Item | Function / Explanation |
|---|---|
| Sobol' Indices | A variance-based measure that quantifies how much of the output variance can be attributed to each input parameter, both alone and through interactions with other parameters [31]. |
| Factorial Design | An experimental design used to study the effects of multiple factors (parameters) by varying them simultaneously. It is efficient for detecting interactions between parameters [32]. |
| Surrogate Model (Meta-Model) | A simplified, computationally efficient model (e.g., a Gaussian Process or polynomial chaos expansion) trained to approximate the input-output behavior of a complex ABM, enabling fast sensitivity analysis [52]. |
| Stochastic Individual Conditional Expectation (S-ICE) Plots | A graphical tool that displays how the predicted output of an ABM changes as a single parameter is varied, with modifications to account for the model's inherent stochasticity [32]. |
| Monte Carlo-Once-At-a-Time (MC-OAT) | A proposed protocol for intelligently exploring an ABM's parameter space to identify regions where the model behavior is well-behaved enough for reliable surrogate modeling [52]. |
Assessing Ulam-Hyers Stability for Continuous Dependence on Inputs
The credibility assessment of computational models through Verification, Validation, and Uncertainty Quantification (VV&UQ) is a cornerstone of reliable in-silico trials for drug development [17]. Within this framework, existence and uniqueness analysis forms a critical first step in the verification of Agent-Based Models (ABMs), ensuring that the mathematical description of a biological system is well-posed and that a unique solution exists for a given set of inputs [7]. This technical note addresses a subsequent, vital aspect of model robustness: Ulam-Hyers stability.
For complex models simulating human pathophysiology, it is not enough to know that a unique solution exists. Researchers must also be confident that a model's output does not change drastically in response to tiny, often unavoidable, perturbations in its inputs or initial conditions. Ulam-Hyers stability provides a formal mathematical framework to quantify this continuous dependence on inputs. A model possessing this stability property ensures that approximate inputs lead to approximately correct outputs, a non-negotiable feature for models intended to inform high-stakes decisions in medicinal product development [53] [54].
This guide provides a technical support framework, in a question-and-answer format, to help researchers and scientists working with ABMs to understand, assess, and troubleshoot issues related to Ulam-Hyers stability within their verification workflows.
Core Concepts & Definitions: The Scientist's Toolkit
What is Ulam-Hyers Stability?
Ulam-Hyers stability formally assesses whether small perturbations in a model's input functions or initial conditions lead to only proportionally small changes in the solution. For a model to be Ulam-Hyers stable, there must exist a positive real number, ( C ), such that for every ( \epsilon > 0 ) and every ( \epsilon )-approximate solution, there exists an exact solution of the model within a distance ( C \times \epsilon ) [53] [54]. This property is crucial for ensuring that numerical approximations and input uncertainties do not invalidate model predictions.
How does it relate to my ABM verification thesis research?
Your thesis research on existence and uniqueness for ABM verification establishes that your model is mathematically sound. Proving Ulam-Hyers stability is the next logical step. It demonstrates that your model is not just mathematically correct but also robust and reliable for practical use. It directly addresses the question: "If my measured initial patient data or model parameters have small errors, will my model's prediction of treatment efficacy remain trustworthy?" [17] [7]. This provides strong evidence for the model's credibility in a regulatory context.
Table: Key Mathematical Concepts in Stability Analysis
| Concept | Formal Definition | Role in ABM Verification |
|---|---|---|
| Ulam-Hyers Stability | For every (\epsilon > 0) and (\epsilon)-approximate solution, an exact solution exists within distance (C \cdot \epsilon). | Quantifies robustness to input perturbations and numerical approximations. |
| Continuous Dependence | A property of a system where small changes in initial data lead to small changes in the solution. | Ensures model predictability and realism, aligning with physical and biological systems. |
| Existence & Uniqueness | Proof that a solution to the model equations exists and is unique for given initial conditions. | The foundational first step of model verification, ensuring the problem is well-posed. |
Troubleshooting Guides & FAQs
FAQ 1: My ABM is stochastic. Can Ulam-Hyers stability, which seems deterministic, still be applied?
Answer: Yes, but the framework must be adapted. The core principle of assessing output sensitivity to input variations remains paramount. For stochastic ABMs, the verification process should be separated into deterministic and stochastic components [17].
- Deterministic Verification: Freeze the random seeds (RSs) used for agent initialization, environmental factors, and other stochastic variables. With the stochasticity removed, you can apply Ulam-Hyers stability analysis to the deterministic core of your model to verify the underlying rules and logic.
- Stochastic Verification: Once the deterministic core is verified, you can analyze the stochastic aspects. This involves running the model multiple times with different random seeds to establish properties like distributional equivalence and to ensure that the statistical distributions of outputs are stable and consistent for a given set of inputs [17].
Troubleshooting Tip: If you find high output variance across random seeds, it may indicate that your model is overly sensitive to stochastic elements. This could necessitate a sample size analysis to determine the number of simulation runs required to establish stable output distributions reliably [7].
FAQ 2: How do I practically test for Ulam-Hyers stability in a complex ABM?
Answer: A practical approach involves a controlled parameter sweep and output analysis, which can be partially automated using tools like Model Verification Tools (MVT) [7].
- Identify Key Inputs: Select the input parameters and initial functions for which you want to test stability (e.g., initial bacterial load, cytokine concentrations).
- Define Perturbation Bounds: Define a realistic range of small perturbations (( \delta )) for each input, based on possible measurement errors or biological variability.
- Generate and Run Simulations: Systematically generate input sets by applying these small perturbations to your baseline inputs. Run your ABM for each perturbed input set.
- Quantify Output Differences: For a key output quantity of interest (e.g., final bacterial count, time to clearance), calculate the difference between the baseline output and the perturbed outputs.
- Establish the Stability Constant: Analyze the relationship between the size of the input perturbation (( \delta )) and the resulting output difference. A stable model will show a bounded, preferably linear, relationship, allowing you to estimate a stability constant ( C ).
Table: Example Protocol for Testing Input Sensitivity
| Step | Action | Tool/Metric |
|---|---|---|
| 1. Input Selection | Choose inputs for testing (e.g., Mtb_Sputum, IL-2). |
Domain knowledge, sensitivity analysis (e.g., LHS-PRCC [7]). |
| 2. Perturbation | Apply small, systematic variations to selected inputs. | Parameter sweep algorithms; MVT [7]. |
| 3. Simulation | Execute the ABM for all perturbed input sets. | Your ABM framework (e.g., UISS-TB [17]). |
| 4. Output Analysis | Compute the difference in a key output metric. | Percentage error, absolute difference, statistical distance. |
| 5. Stability Assessment | Model the input-output error relationship to find constant ( C ). | Linear regression, worst-case analysis. |
FAQ 3: My analysis shows the model is not Ulam-Hyers stable. What are the common culprits?
Answer: Instability often points to underlying structural or implementation issues in the model. Common culprits include:
- Ill-Conditioned Parameters: Certain parameter combinations may cause the model to bifurcate or behave chaotically. A parameter sweep analysis is essential to identify these ill-conditioned regions of your input space [7].
- Violation of Model Assumptions: The model might be operating outside the physiological range for which it was designed. Revisit the assumptions and boundaries of your model's validity.
- Numerical Instability: The chosen time-step or numerical solvers might be inappropriate. Conduct a time-step convergence analysis to ensure your numerical solution is accurate and that reducing the time-step does not significantly change the output [17] [7].
- Stiffness and Discontinuities: The model dynamics may contain very fast and very slow processes, leading to "buckling" or sharp transitions in output. A smoothness analysis, which calculates the coefficient of variation of the first difference of the output time series, can help detect such issues [7].
FAQ 4: How do I visually represent the relationship between solution concepts and stability?
Answer: The logical pathway from fundamental verification to advanced stability properties can be mapped as a workflow. The following diagram illustrates the dependency of Ulam-Hyers stability on prior verification steps, particularly existence and uniqueness.
Diagram 1: ABM Verification Pathway
Experimental Protocols & Data Presentation
Detailed Methodology: Time-Step Convergence Analysis
A critical prerequisite for stability analysis is ensuring that numerical errors from time discretization are minimal. The following protocol is adapted from established ABM verification procedures [17] [7].
Objective: To verify that the numerical solution of the ABM is not overly sensitive to the choice of time-step (( \Delta t )), and to identify a sufficiently small ( \Delta t ) for accurate simulations.
Procedure:
- Select a Reference Time-Step: Choose a very small time-step (( \Delta t_{ref} )) that is computationally expensive but can be considered a surrogate for the "true" solution.
- Define Coarser Time-Steps: Select a series of progressively larger time-steps (( \Delta ti )) for testing (e.g., ( 2\times, 5\times, 10\times ) of ( \Delta t{ref} )).
- Run Simulations: Execute the ABM with the same initial conditions and parameters for the reference and all coarser time-steps.
- Calculate Discretization Error: For a key output quantity (( q )), such as the peak value or final value of a critical variable, compute the percentage discretization error for each time-step: ( e_{q}^{i} = \frac{| q^{i} - q^{ref} |}{| q^{ref} |} \times 100 ) where ( q^{ref} ) is the output from the reference time-step and ( q^{i} ) is the output from a coarser time-step.
- Establish Convergence: A model is considered converged when the error ( e_{q}^{i} ) falls below a pre-defined tolerance (e.g., 5% as suggested in [7]).
Table: Exemplar Time-Step Convergence Data
| Time-Step (( \Delta t )) | Output (( q )) | Discretization Error (( e_q \% )) | Convergence Status |
|---|---|---|---|
| 0.001 (Ref) | 1045.2 | 0.0% | Reference |
| 0.01 | 1041.7 | 0.33% | Converged |
| 0.1 | 1025.8 | 1.85% | Converged |
| 0.5 | 995.3 | 4.77% | Converged |
| 1.0 | 901.6 | 13.74% | ✘ Not Converged |
Key Research Reagent Solutions
The following table details essential computational "reagents" and their functions in conducting the analyses described in this guide.
Table: Essential Computational Tools for ABM Verification & Stability Analysis
| Tool / Resource | Type | Primary Function in Verification |
|---|---|---|
| Model Verification Tools (MVT) [7] | Software Toolkit | Automates key verification steps: time-step convergence, smoothness analysis, and parameter sweep. |
| UISS-TB Model [17] | Agent-Based Model | An exemplary, well-documented ABM of the human immune response to tuberculosis, used in mission-critical in-silico trials. |
| Pseudo-Random Number Generators (MT19925, TAUS2) [17] | Algorithm | Provide controllable stochasticity, allowing separation of deterministic and stochastic verification via fixed or varying random seeds. |
| Latin Hypercube Sampling (LHS) [7] | Sampling Technique | Efficiently explores the multi-dimensional input parameter space for sensitivity and parameter sweep analyses. |
| Partial Rank Correlation Coefficient (PRCC) [7] | Statistical Metric | Quantifies the monotonic influence of individual input parameters on model outputs, identifying key drivers of sensitivity. |
Establishing Credibility for High-Fidelity and High-Stakes Models
Troubleshooting Common Model Verification Issues
This section addresses frequent challenges researchers encounter when verifying high-fidelity Agent-Based Models (ABMs).
| Problem Area | Specific Issue | Diagnostic Steps | Recommended Solution |
|---|---|---|---|
| Mathematical Consistency | Coupling discrete stochastic ABM with continuum PDEs creates instability [27]. | Check for violation of conservation laws; Analyze discretization vs. sampling errors [27]. | Implement hybrid numerical schemes that control combined errors; Use moment-closure methods for tractable PDE descriptions [27]. |
| Model Documentation | Incomplete model description prevents replication and validation [55] [56]. | Use the ODD (Overview, Design concepts, Details) protocol as a checklist [56]. | Document the model thoroughly using the ODD protocol, including purpose, entities, state variables, process overview, and submodels [55] [56]. |
| Spatial Structure & Heterogeneity | Model fails to capture policy resistance or emergent dynamics from adaptation [57]. | Test if outcomes are robust across heterogeneous agents and co-evolving environments [57]. | Explicitly model individual actors without aggregation; Incorporate rich spatial data (e.g., GIS) and social networks [57]. |
| Stochastic Analysis | Inability to connect microscale randomness to macroscopic dynamics [27]. | Compare model output against derived mean-field PDE limits [27]. | Use exact stochastic algorithms (e.g., Gillespie) for transitions; Derive analytically tractable continuum limits from discrete rules [27]. |
| Visualization & Communication | Visualizations are ineffective, making model behavior hard to understand [25]. | Review visualizations for cognitive efficiency and aesthetic design principles [25]. | Apply design techniques from Gestalt psychology and scientific visualization to simplify and emphasize the model's key message [25]. |
Frequently Asked Questions (FAQs)
What is the single most critical element for establishing model credibility in a hybrid PDE-ABM system?
For coupled PDE-ABM systems, the most critical element is providing a rigorous existence and uniqueness analysis for the coupled system. This mathematical proof establishes that the model's equations are well-posed, meaning solutions exist, are unique, and depend continuously on the initial data, which is foundational for all subsequent verification and validation [27].
How can I ensure my ABM is described well enough for another researcher to replicate it?
Adopt a standardized documentation protocol. The ODD (Overview, Design concepts, Details) protocol is widely accepted for this purpose. It ensures you provide a consistent, logical, and complete account of the model's structure and dynamics, covering elements like purpose, entities, state variables, process overview, scheduling, and detailed submodels [55] [56].
Our model produces unrealistic results after many simulation steps. How should we troubleshoot this?
This often indicates issues with scheduling or emergent adaptation. First, verify the order of operations in your "Process Overview and Scheduling" (Element 3 of ODD). Second, analyze whether adaptive agent behaviors or interactions with a co-evolving environment are producing policy-resistant dynamics. Using the "Design Concepts" element of ODD as a checklist can help identify the root cause [57] [56].
How do we validate a stochastic ABM against real-world data when the mean-field limit is available?
A two-pronged approach is most effective:
- Compare against the Mean-Field Limit: Ensure the average behavior of multiple stochastic simulations converges to the deterministic mean-field PDE you derived. This validates the core mathematical connection between micro-scale rules and macro-scale dynamics [27].
- Compare against Observational Data: Check if the statistical distribution of outcomes from your stochastic simulations matches the variance and patterns found in real-world data, ensuring the model captures appropriate levels of uncertainty and heterogeneity [57].
Experimental Protocols for ABM Verification
Protocol 1: Establishing Mathematical Well-Posedness for Hybrid PDE-ABM Systems
Purpose: To provide a rigorous foundation for a hybrid model by proving existence and uniqueness of solutions [27].
Workflow:
Methodology:
- System Formulation: Precisely define the coupled system, specifying all PDE components (e.g., reaction-diffusion equations for oxygen, drug, TAF) and ABM components (e.g., stochastic rules for endothelial cell migration, tumor cell phenotype switching) [27].
- Functional Setting: Place the system within an appropriate function space (e.g., Banach space) that can handle both the continuum fields and stochastic elements.
- Existence/Uniqueness Proof: Apply fixed-point theorems (e.g., Picard-Lindelöf) or variational methods tailored to hybrid systems. This may involve demonstrating Lipschitz continuity of the coupled operators [27].
- Mean-Field Derivation: Use moment-closure methods to derive a continuum limit PDE from the stochastic agent rules, formally linking the micro-scale ABM to a macro-scale description [27].
Protocol 2: ODD Documentation for Replication
Purpose: To create a complete and unambiguous model description that enables replication and critical evaluation [56].
Workflow:
Methodology:
- Overview (Elements 1-3): Start with the model's purpose and the key patterns it aims to explain. List all entity types (e.g., tumor cells, vessel agents), their state variables, and the model's temporal/spatial scales. Provide a high-level overview of processes and their scheduling [56].
- Design Concepts (Element 4): Explicitly describe how key ABM design concepts are implemented. This includes agent decision-making, adaptation (e.g., learning, phenotype switching), objectives, interaction patterns (e.g., networks, spatial proximity), and how stochasticity is incorporated [57] [56].
- Details (Elements 5-7): Specify initial conditions, any input data from external sources, and provide exhaustive details for each submodel. This includes precise equations, logical rules, and probability distributions governing agent behaviors and interactions [56].
The Scientist's Toolkit: Research Reagent Solutions
| Item | Function in ABM Verification & Analysis |
|---|---|
| ODD Protocol | A standardized template for documenting ABMs. Ensures completeness, facilitates replication, and serves as a design checklist, directly supporting model credibility [55] [56]. |
| Mean-Field Analysis | A mathematical technique to derive a continuum-limit PDE from stochastic agent rules. Connects micro-scale randomness to deterministic macro-dynamics, providing a key check for internal consistency [27]. |
| Gillespie Algorithm | An exact stochastic simulation algorithm. Used to model discrete, random events (e.g., phenotype switching, mutation) within an ABM, ensuring a rigorous representation of biochemical or cellular processes [27]. |
| Moment-Closure Methods | Techniques to approximate higher-order statistical moments to obtain a closed, tractable PDE description from stochastic agent dynamics. Essential for deriving mean-field limits [27]. |
| Hybrid Numerical Schemes | Specialized computational solvers that selectively retain full ABM detail in critical regions while using efficient PDE surrogates elsewhere. Balances accuracy and computational cost in coupled systems [27]. |
| Cognitive Visualization Design | The application of principles from Gestalt psychology and graphic design. Creates clear and understandable ABM visualizations that help identify, communicate, and understand emergent model behavior [25]. |
Conclusion
Existence and uniqueness analysis is not an abstract mathematical exercise but a foundational pillar for constructing trustworthy Agent-Based Models in biomedical research. This article has synthesized a clear pathway from foundational principles through practical application, troubleshooting, and final validation. By systematically implementing these verification steps, modelers can significantly enhance the robustness and regulatory credibility of their in silico tools. The future of ABMs in drug development and personalized medicine hinges on such rigorous practices. Promising directions include the development of more automated verification software, the formal integration of these concepts with hybrid PDE-ABM frameworks, and the establishment of standardized verification protocols for specific clinical applications, ultimately accelerating the adoption of in silico evidence in regulatory decision-making.
References
- 1. Existence and uniqueness of solutions for stochastic ... [https://www.aimspress.com/article/doi/10.3934/math.20241099]
- 2. Agent-Based Model (ABM) validation considerations [https://www.rti.org/publication/agent-based-model-abm-validation-considerations]
- 3. A Bibliography of ABM Research Explicitly Comparing ... [https://rofasss.org/2020/06/12/abm-validation-bib/]
- 4. Text has enhanced contrast | ACT Rule | WAI [https://www.w3.org/WAI/standards-guidelines/act/rules/09o5cg/]
- 5. In silico trials: Verification, validation and uncertainty ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC7883933/]
- 6. A Credibility Assessment Plan for an In Silico Model that ... [https://link.springer.com/article/10.1007/s10439-022-03078-w]
- 7. Model verification tools: a computational framework for ... [https://bmcbioinformatics.biomedcentral.com/articles/10.1186/s12859-022-04684-0]
- 8. In silico trials: Verification, validation and uncertainty ... [https://www.sciencedirect.com/science/article/pii/S1046202319302452]
- 9. Empirical Validation and Verification of Agent-Based Models [https://faculty.sites.iastate.edu/tesfatsi/archive/tesfatsi/EmpValid.htm]
- 10. Agent‐Based Modeling in Systems Pharmacology - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC4716580/]
- 11. a critical review of LLMs in agent-based modeling [https://link.springer.com/article/10.1007/s10462-025-11412-6]
- 12. Agent-based modeling in cancer biomedicine - PubMed Central [https://pmc.ncbi.nlm.nih.gov/articles/PMC11057625/]
- 13. Existence and Uniqueness of Some Unconventional ... [https://www.mdpi.com/2504-3110/8/3/148]
- 14. AgentGuard: Runtime Verification of AI Agents [https://arxiv.org/html/2509.23864v1]
- 15. High-Fidelity Agent-Based Modeling to Support Prevention ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8591590/]
- 16. Validation in agent-based models: An investigation on the ... [https://www.sciencedirect.com/science/article/abs/pii/S0167268107001722]
- 17. Verification of an agent‐based disease model of human ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC8365724/]
- 18. Existence and Uniqueness Results for a Class of Fractional ... [https://www.mdpi.com/2504-3110/9/1/42]
- 19. Mobile Verification Toolkit [https://mvt.re/]
- 20. Introduction [https://docs.mvt.re/en/latest/introduction/]
- 21. MVT (Mobile Verification Toolkit) helps with conducting ... [https://github.com/mvt-project/mvt]
- 22. Color palettes and accessibility features for data ... - Medium [https://medium.com/carbondesign/color-palettes-and-accessibility-features-for-data-visualization-7869f4874fca]
- 23. How can I set a text color to always contrast with the fill ... [https://stackoverflow.com/questions/62800823/how-can-i-set-a-text-color-to-always-contrast-with-the-fill-color-of-a-chart]
- 24. [solved] How to use fillcolor attribute? - Help [https://forum.graphviz.org/t/solved-how-to-use-fillcolor-attribute/2637]
- 25. Design Guidelines for Agent Based Model Visualization [https://www.jasss.org/12/2/1.html]
- 26. In silico trial to test COVID-19 candidate vaccines [https://pmc.ncbi.nlm.nih.gov/articles/PMC7733700/]
- 27. Analysis and Mean-Field Limit of a Hybrid PDE-ABM ... [https://www.mdpi.com/2227-7390/13/17/2898]
- 28. Analysis and Mean-Field Limit of a Hybrid PDE-ABM ... [https://www.preprints.org/manuscript/202508.0408/v1]
- 29. Brief introductory guide to agent-based modeling and an ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5391997/]
- 30. Configuring a Parameter Sweep Analysis in Multisim - NI [https://knowledge.ni.com/KnowledgeArticleDetails?id=kA03q000000YH8FCAW&l=en-US]
- 31. Which Sensitivity Analysis Method Should I Use for My ... [https://www.jasss.org/19/1/5.html]
- 32. Sensitivity analysis of agent-based models: a new protocol [https://link.springer.com/article/10.1007/s10588-021-09358-5]
- 33. What Can Mathematics Do for Drug Development? - PMC [https://pmc.ncbi.nlm.nih.gov/articles/PMC6722144/]
- 34. Parametric Sweep - an overview [https://www.sciencedirect.com/topics/engineering/parametric-sweep]
- 35. LTspice: AC Analysis Using The Step Command [https://www.analog.com/en/resources/technical-articles/ltspice-ac-analysis-using-the-step-command.html]
- 36. 应对较小自动时间步的策略 [https://cn.comsol.com/blogs/strategies-to-counter-small-automatic-time-steps]
- 37. 有限差分法- 維基百科,自由的百科全書 [https://zh.wikipedia.org/wiki/%E6%9C%89%E9%99%90%E5%B7%AE%E5%88%86%E6%B3%95]
- 38. 23、显式时间离散化方法详解原创 [https://blog.csdn.net/uber9/article/details/150804604]
- 39. 数值直线方法 [https://reference.wolfram.com/language/tutorial/NDSolveMethodOfLines.html.zh]
- 40. Taming Randomness in Agent-Based Models using ... [https://arxiv.org/html/2409.02086v1]
- 41. Replicability, Reproducibility, and Agent-based Simulation ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC5977631/]
- 42. Improving policy-oriented agent-based modeling with ... [https://www.sciencedirect.com/science/article/pii/S1755436525000337]
- 43. Leveraging agent-based models and deep reinforcement ... [https://www.nature.com/articles/s41540-025-00576-0]
- 44. An efficient and flexible framework for inferring global ... [https://journals.plos.org/ploscompbiol/article?id=10.1371/journal.pcbi.1013427]
- 45. A Simple Framework for Agent-Based Modeling with ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC11821717/]
- 46. A Method for Validating and Discovering Associations ... [https://link.springer.com/chapter/10.1007/978-3-540-78582-8_1]
- 47. Agent-based modeling: Methods and techniques for ... [https://pmc.ncbi.nlm.nih.gov/articles/PMC128598/]
- 48. Verification & Validation of Agent Based Simulations using ... [https://arxiv.org/abs/1708.02361]
- 49. Agent-based services for the validation and calibration of ... [https://www.sciencedirect.com/science/article/abs/pii/S0198971508000616]
- 50. Quantitative systems modeling approaches towards ... [https://www.frontiersin.org/journals/systems-biology/articles/10.3389/fsysb.2022.1063308/full]
- 51. Theory for and from agent-based modelling: Insights from a ... [https://www.sciencedirect.com/science/article/pii/S136481522400149X]
- 52. Modern Tools for Agent-Based Model Sensitivity Analysis [https://papers.ssrn.com/sol3/papers.cfm?abstract_id=4689174]
- 53. Continuous Dependence on the Initial Functions and ... [https://www.mdpi.com/2504-3110/7/10/742]
- 54. Existence and Ulam-Hyers-Rassias stability of mild ... [https://www.aimsciences.org/article/doi/10.3934/mfc.2023053]
- 55. Documentation and Standards for ABMs [https://modelsen.gea.mpg.de/tutorials/abm_intro/ch3_practice/documentation.html]
- 56. The ODD Protocol for Describing Agent-Based and Other ... [https://www.jasss.org/23/2/7.html]
- 57. Considerations and Best Practices in Agent-Based Modeling ... [https://www.ncbi.nlm.nih.gov/books/NBK305917/]